 Following close on the heels of the Lenovo “Superfish” debacle comes news of yet another major manufacturer embroiled in similar security controversy, this time it’s the US-based Dell.
Following close on the heels of the Lenovo “Superfish” debacle comes news of yet another major manufacturer embroiled in similar security controversy, this time it’s the US-based Dell.
As part of an enhanced support tool, Dell installed a self-signed root certificate (eDellRoot) and corresponding private key on its computers, apparently blissfully unaware that this exposes users’ encrypted communications to potential spying. Even more surprising is that the company did this with full knowledge of Lenovo’s very similar security blunder which came to light earlier this year.
In Lenovo’s case the goal was ad injection whereas Dell asserts that it was only trying to streamline remote support. Regardless of intention, this silly blunder creates a gaping security hole for those affected.
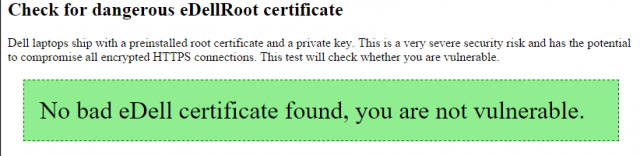
At this stage it remains unclear as to exactly what models may be affected. However, Dell PC owners can check for the vulnerability here: https://edell.tlsfun.de/
(NOTE: Firefox is not vulnerable because it maintains its own certificate store – the test should be performed using Internet Explorer, Edge, or Chrome).
*A second rogue certificate (DSDTestProvider) has also been uncovered but it is not preloaded and only installed if/when a customer chooses to proactively download the Dell System Detect software. According to Dell… “the impact from Dell System Detect is limited to customers who used the “detect product” functionality on our support site between October 20 and November 24, 2015″
Dell has confirmed the existence of the rogue certificates and provided instructions on how to permanently remove them:
- Dell’s admission: Response to Concerns Regarding eDellroot Certificate
- Dell’s removal instructions: How to remove the eDellRoot and DSDTestProvider certificates from your system
NOTE: For those who may find Dell’s instructions a tad overwhelming, Major Geeks has provided a download to automatically remove the certificate here: eDellRoot Certificate Fix
*Dell also commenced pushing a software update on November 24 that will check for the certificate, and remove it if detected.


So this is just laptops not desktops? Includes alienware? thx.
The first thing I did with my Dell is to get the Windows Product key and download a Windows Iso from Microsoft. Then I did a clean install. It is easy to download the drivers that are needed from Dell after the install. Gets rid of all the crapware and useless Dell software at the same time.
“blissfully unaware that this exposes users’ encrypted communications to potential spying.”
lol….bollocks! it’s painfully obvious that was done by design. to MAKE it easier to spy on you.
The line actually reads…”apparently blissfully unaware that this exposes users’ encrypted communications to potential spying“.
Apparently you missed the “apparently”, which indicates a note of sarcasm. If you’re going to quote a line from the article, at least quote it accurately and not an edited version.