Sadly, major websites get hacked often enough to warrant repeated coverage on mainstream news. Wondering if you’re listed in the Ashley Madison data dump? Has your Gmail password been leaked without your knowledge? Did you notice when 145 million details were stolen from Ebay? Curious? I am…
The internet has lead to almost every website asking for passwords to carry out basic actions, such as complete a purchase or get support. As a result most internet users rely on either one password, or one main password with derivations thereof. As a security researcher I can understand the propensity towards a single password system. It’s quick and easy to remember, but it could be better.
I have a tip that could make even the weakest password infinitely more secure. For most people following the simple rule below is enough to exponentially increase password entropy, without the effort of remembering random strings of junk that some mistakenly call a secure password. What is this magic rule? Simple…
Password Entropy
The top tip is: Don’t be predictable!
Entropy is synonymous with randomness, or the “lack of order or predictability“. There is a very easy way to increase the entropy of any password: make it longer. Password checks are binary. That is to say there are two answers. Yes or no &mdashl correct or not. When entering a password the computer (almost) never says “Nearly. Try adding a number near the end.”. The response is usually something along the lines of: “Password incorrect.”
Making a password longer doesn’t mean it has to be more difficult to remember. I often cite this example, because it’s weird and wonderful:
Which of the following two passwords is stronger,
more secure, and more difficult to crack?
D0g.....................
Or
PrXyc.N(n4k77#L!eVdAfp9
Of course this is a trick question. The former (first) password is, contrary to common sense, the stronger of the two because of interpreted entropy enforced by cracking algorithms. Making a password longer helps and it doesn’t need to be random noise to be more secure than your dog’s real name.
You just need to find a mnemonic that works for you.
Password faux-pas
I deal with passwords every day, as a freelance programmer and website marketer. A few days ago I had to change a password from the name of the town in which the company resides. Below is a list of issues is often see with password creation techniques.
- Commonly used passwords
- Predictability
- Dates, of any kind
- Details about family
- Business details
- Hobbies
- Any dictionary word
I always suggest avoiding anything in the list above for obvious reasons. Again, the magic word is predictability.
Long-term Password Security
If you manage a lot of login details and want a better solution then there is help. Several password managers are available for all popular browsers. If you consider a password manager as an option, I always recommend checking for yourself to see if it’s been audited and exactly how secure it is. Your password manager password really is the one ring to rule them all. Get access to that and you can reset access to any associated account.
I have always used and recommended LastPass. It’s been audited, appears to be secure, and was recently hacked. Yep, that’s right. I’m recommending a password manager that was hacked recently. They implement pre-egress encryption which uses uses 10,000 iterations of a PBKD to individually salt passwords. If you read the rest of this article you may see where this is going — if your LastPass password was unpredictable, then your data was safe.
There are many alternatives to LastPass, but I have not personally audited them. Some are great and some are terrible. A little research is required before trusting them with the keys to your kingdom.
An Alternative
So, passwords aside, where are we headed? There is a technology in development called SQRL — Secure Quick Reliable Login. The idea is simply to replace passwords with a QR code that creates a unique, but anonymous, identifier which can be used to login. The QR code can be scanned using a mobile device or clicked in the browser. 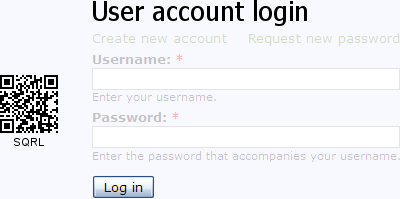
The cryptographic security has been scrutinised. Hackers and coders alike have trawled the code, and it looks good. I predict it will start fairly small but gain traction as a viable alternative to 3rd party logins, such as Facebook and Twitter. Steve Gibson gained notoriety for coining the term spyware and subsequently creating the first anti-spyware program, called OptOut.
Have I been “PWND”?
Until SQRL is ready we have to be diligent. You can check the Breach Or Clear website to see if your details have been leaked. It’s an easy way to search 53 major breaches containing 220,209,727 compromised accounts.


To make passwords easy, I use keystroke patterns, instead of words, dates or phrases. This allows me to apply a single pattern anywhere on the keyboard, and have a different password for almost every login.
So, using only 4 key positions at a time on the keyboard, I can create a unique 13 character password of seemingly random order for virtually every different online login that I have. The login passwords for some online accounts may be the same, depending on the letters, and the order of those letters, in their domain name. But, I can have over 3 dozen different login passwords (patterns) for all my different logins, using a combination of alpha-numerical and UPPER/lower case patterns.
So, for example, using Microsoft’s password predicting site (https://telepathwords.research.microsoft.com/), using only the keys F f G g r t, only 3 of 13 character in the password are predicted. Okay, since I use the Shift key in the keystroke pattern, I am technically using 6 different keys. But, I’m only using 4 positions on the keyboard, which makes my pattern very easy to remember. And, I can apply the pattern in many different places on the keyboard. I don’t use special character keys, since some sites don’t allow special characters in their passwords. But, I could if using special characters in passwords was more universal.
Try it yourself. Go to the Telepathwords site and try making a 13 character password that you can repeat over and over again, and have no more than 3 of your keystrokes predicted by the Microsoft password prediction engine. You can use only 4 key positions. But, you can use the Shift key to change the character to upper or lower case. For the sake of simplicity, you can use 4 keys that are adjacent to each other. Such as, FVGB.
(Tip: On the Telepathwords site, uncheck the box for “Donate my keystrokes to science”. No need to give MS the secret to your chosen pattern.)
With this keystroke pattern method of creating passwords, I never need to store my passwords anywhere. All I have to do is remember two things… the one keystroke pattern I use, and where on the keyboard to start the pattern. Where I start the pattern is based on the letters in the domain name. I have a rule for which letter in the domain name sets the starting position on the keyboard.
It’s brilliantly simple, and effective.
Thanks for the feedback beachboy. That’s a great tip… Why have I never heard it before? Simple but effective. I love it! I think I’ll try and incorporate it into my current password system. Thanks again, best comment I’ve read in a while 🙂
Using this password technique in the WolframAlpha widget on this site (https://davescomputertips.com/check-your-password-strength/), with only a 10 keystroke password, it would take 13,452 years to hack the password at the rate of 1M guesses per second. My password patterns are typically 12 to 13 keystrokes. I don’t think I’ll be PWNED anytime soon. 😉
Adam, thanks for the post. I have a question about brute force password hacking techniques which you allude to and Steve Gibson and others talk about when advocating longer passwords. Sorry if off-post but I can’t find the answer on the sites I have visited. Do brute force attacks actually require (multiple) attempts to login to the appropriate site – or can the attacks be done entirely “off-line”?
Usually, yes. Hackers bruteforcing a website using something like AccessDiver / Cain & Able would be shown in the logs. This can be somewhat obfuscated by techniques such as proxy rotation to make it harder to tell what attempts are authentic. There are some more esoteric vectors, such as out-of-band attacks, which can bypass the logging process but they aren’t widely used and tend to be more NSA style hacks.
Thanks – in which case won’t their efforts be thwarted by robust protocols relating to failed login attempts? Surely any site concerned about security should reject / report failed login attempts once a certain number has been reached?
Many methods look to IP addresses as the defining signature of an attack, though they can be proxied, and block based on the number of times an IP has been seen (and failed of course).
True, but unfortunatly most websites use a soft limit which has a time based reset or is restet if the user logs in. An example being: 10 failed login attempts in 30 minutes will put a 24 hour ban on the account. Knowing the limits makes bypassing them very easy.
WordPress is a great example as, by default, it comes with almost no protection against such an attack. https://codex.wordpress.org/Brute_Force_Attacks
Many modern content management systems don’t handle incorrect login attempts properly as getting the balance between security and usability is incredibly difficult. Using a service such as CloudFlare is probably the best form of protection.