“Pwnd” – What the Heck Is That?
The etymology of the word ‘pwned’ is not entirely known. There are many speculations about its origin and no one seems to agree on its pronunciation either. The only thing I can find that makes sense is this definition at Wiktionary: “own, possibly born out of a typographical error (o being adjacent to p on qwerty keyboards)” This is a generous speculation. My personal thought is that we have spent a fortune on school systems that merely propagate generations of kids who can’t spell.
Its meaning, on the other hand, is perfectly clear: “to be beaten by a wide margin”
You can’t get on the Internet these days without seeing an article about how this or that major corporation was hacked and lost millions of social security numbers, credit card information, or some other type of personal data that affected many, many people. It is disgraceful behavior.
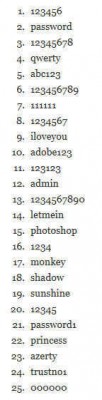
The Worst Passwords of 2013 – The A-List:
The following is a list of the worst passwords of 2013. It was published by a security consulting firm, Stricture Consulting Group, in November 2013 after the Adobe fiasco. Have a look:
All I can say is this, and I am forced to quote Mr. T, ” I pity the poor fool…” If your password is on this list, you are not giving due respect to the cleverness of the bad guy.
Check If You Have Been Pwned
There are many sites on the Internet that now offer you the option of checking if your eMail or password has been compromised. You even have to be careful about them!
Some are just there to trick you into divulging the very information you are trying to protect. Others are eMail “farms”; they are only interested in getting your address so they can sell it to marketing companies.
I will suggest a site called HaveIBeenPwned which has already been the subject of a previous article by fellow author Jim Hillier, you can catch up with Jim’s article here: Has Your Password Been Compromised – Check Now!
Unfortunately, we don’t have a way to 100% verify the site’s integrity other than by trusting the advice from reliable sources, plus from specialist services such as WOT and McAfee SiteAdvisor, both of which rate the site Green (safe). For my part, all I can tell you is that I went there, entered some information, and got some seemingly valid results. I can vouch for the results in one instance that I know is true of an eMail breach at Adobe. Yep! My most UN-favorite company.
Once there, you can enter an eMail address or Username. It will then search a database compiled by consolidating the publicly available major hacks that have occurred on the internet. If your information is found, you will be shown a window including the pertinent status such as the site, eMail, and/or Username. It may also display some password hints that you have entered as well.
What To Do If You Have Been Pwned
Immediately go to the offending site and change your password. When it comes to password hints, I suggest lying. I know your parents told you never to do this, but in this case I say, “Defy them.”
Don’t give them your mother’s real maiden name. Make something up like your parrot’s favorite swear word. A maiden name can easily be discovered on the likes of Google or any other search engine worth its salt. Be creative.
Password Management
To be sure, the best way at this time to protect yourself is to have a strong password– certainly not something from the aforementioned bad passwords list.
You want to have at least a 14-character password (the longer the better) and one that contains a variety of characters including lower and upper case characters, numbers and the so-called special characters like the dollar sign, caret, ampersand and so forth. Be creative.
Obviously, the problem with these complex passwords is that no normal person can remember them all. The best practice is to have a unique password for every site at which you have an account. In my case, that’s in the hundreds.
I am not “The Rain Man” and don’t immediately know how many toothpicks fell on the floor nor can I memorize an entire phone book at a glance. I must depend on a good, secure password manager to handle this. I won’t go into the numerous options here but I do recommend that you take a look at LastPass. You may install it as a desktop application or as an add-on in all the major browsers. I prefer the latter.
Final Thoughts
These days, the security considerations of traversing the very dangerous Internet are not a luxury– they are an absolute necessity.
Poor excuses for passwords such as “123456” or the very clever “asdf” (look at your keyboard) can be “cracked” by the nefarious among us in the blink of an eye.
There are creatures ‘out there’ that do this for a living and they’ve become very adept at their endeavors. They also have the computing power to sustain their nasty behavior– probably garnered with money they have already stolen from other unsuspecting innocents.
Just because they are crooks does not mean they are stupid. To the contrary, they are intelligent, well-equipped criminals who want your hard-earned cash and will stop at nothing to attain that goal.
Keep this terrible news in your fore-thoughts and please begin by making an effort to protect yourself with a good password regimen at all the sites you visit. Doing so will not guarantee your security, but it is certainly a huge step in the right direction.
It will only get worse, so beware the stranger bearing gifts and start the new year with a big electronic stick,
Richard
—






Best advice ever, to everyone, is Last Pass. Changing the password is also an amazing tip.
Hi Megaman,
Glad you found it helpful and thanks for the kind comments,
Richard
Hi Richard,
I like your comment, “””””we have spent a fortune on school systems that merely propagate generations of kids who can’t spell.””””””
Now, relating to safe passwords, I have given up, finished, the end of advising clients, friends and family about the dangers, (stupidity) of using simple passwords, and some with one password for every account, unbelievable!
Regards,
JoninOz
Hi JoninOz,
It does get tiring having to repeat the same old caveats over and over again, but we must persevere. Think of it as job security.
Apparently, they aren’t scared enough yet. Their day will come and they will wish they had listened to that Strong Password in the Sky. We’ll know when that happens because there will be all those whining and sniveling sounds surrounding us. That’s when I start charging the big bucks. No mercy!
Hang in there 😉
Richard