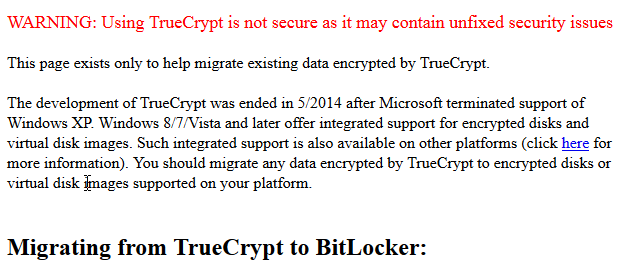
TrueCrypt, the most popular free and open source encryption software, has abruptly changed its homepage to display a message saying that the software is not secure and suggesting that existing users should migrate to Bitlocker:
 As you can imagine, the net is abuzz with news of this strange message. Some are saying that, because it was so sudden, the website must have been hacked. The consensus among most security experts however, is that the new page and its message are genuine. If that is indeed the case, then it’s probably safe to assume that TrueCrypt has been compromised in some way.
As you can imagine, the net is abuzz with news of this strange message. Some are saying that, because it was so sudden, the website must have been hacked. The consensus among most security experts however, is that the new page and its message are genuine. If that is indeed the case, then it’s probably safe to assume that TrueCrypt has been compromised in some way.
At the moment there are more questions than answers – Is it hackers? Is the NSA involved? Has the audit team found something sinister? – It’s all speculation though and no-one really knows what’s going on for sure. It doesn’t help that the developers are a secretive and anonymous bunch either.
It does seem kind of strange for open source connections to be promoting something as closed source as Bitlocker though, especially when Microsoft’s encryption tool is not available on basic Windows versions, including the popular and widespread Home editions.
Matthew Green, one of the security researchers involved with the TrueCrypt audit, has Tweeted that he believes the announcement is legitimate. So it would appear unlikely that a sinister audit finding is at the core.
A new version of the software, which was released simultaneously with the announcement, no longer supports encryption, but simply allows users to decrypt. Most security experts are labeling this latest version ‘suspicious’ and advising users NOT to download it.
Software developer Jonathan Zdziarski, who worked as a cryptographer on the TrueCrypt project Tweeted a warning against using the new version – or any recent version, for that matter… “If TrueCrypt.org is compromised, it’s likely been compromised a good while. I wouldn’t trust any recent downloads of the software.”
It makes for a difficult situation when the reality is so obscure, and until more reliable information comes to hand, the rumors and speculation will remain just that.

It is indeed a very strange story…
I must say I was a bit concerned one day this could happen, not in this way though.
I used to keep all my emails and the data from 1Password (an app that stores all passwords and even credit card details) in encrypted files on DropBox, which was a bit silly in my part. I took them down fearing that, even though no backdoors were known at that time, one could obtain the data and just wait for a time in which a vulnerability was found.
Seems like it didn’t take that long…
I have been using True Crypt for several years. Is the True Crypt Volume I created still secure?
This is devastating news for people who value security. Bit-Locker and the like are corporate programmes that will cave under pressure from authorities. The also generally have password only encryption while Truecrypt offered multiple layers allowing combinations of key files and/or passwords. You do not have to be a criminal to need security, in some countries you might want to keep things or share things that could land you in serious trouble because of some political or religious factor. Truecrypt had an ace up its sleeve which was hidden protected drives which allowed you to reveal a password to access some data while keeping sensitive data completely hidden. Some governments have the power to invade your privacy by making non revealing a password an offence. The theory was that there was nothing on the system to indicate that there was any other encrypted data other than what you chose to reveal.
It is not particularly important to me personally but is a serious blow to the whole concept of privacy on the internet and one we should all be concerned about. I do not trust any private company not to be in league with the US government.
Has it become unsafe or have the website owners been pressured into making people feel unsafe – time will tell?
My favorite:
Take the first letters of the warning words: “uti nsa im cu si”. Put the result in the google translator – from Latin to English, you receive…’If I wish to use the NSA’. LOL
You should read this https://www.grc.com/misc/truecrypt/truecrypt.htm and http://truecrypt.ch/ (a site dedicated to reviving true crypt based in neutral Switzerland which is free of both US and EU intervention)
This is good info Clive. Steve Gibson is a very trustworthy source. The Swiss connection looks promising too.
Hi Jim. What is meant by being insecure? I have a password protected True Crypt volume I use.
Nobody really knows Daniel. All we know is that the TrueCrypt development team labeled their software as “not secure”, they did not expand on the reasons.
Steve Gibson, respected security expert, has asserted that the software “is still safe to use” saying that the original TrueCrypt development team no longer wanted to carry on but they also didn’t want anyone else to take the project over, so they concocted the “not safe” scenario.
However, Mr. Gibson has not provided any definitive proof one way or the other and while I respect Mr. Gibson and his expertise, and he may well be correct, under the circumstances his statement does appear to be pretty bold.
Hi Jim. I for one will continue to use my True Crypt Volume. I keep it on another drive but will probably move it to my external drive and access from their. I have tried bitlocker and do not really car for it. Daniel.
It depends what you use it for – if it is just keeping family members out of certain content then I don’t think it is anything to worry about. If it is a question of national security then that might be different. It is working as a local programme and no reason for it not to continue working – whether it would be safe if the NSA hacked into your PC is another matter but then it is not going to be any more safe from them by using something else
Hi Clive. Nothing CIA critical. Just some personal info. Thanks Daniel.