Phishing: is the attempt to obtain sensitive information such as usernames, passwords, and credit card details (and, indirectly, money), often for malicious reasons, by disguising as a trustworthy entity in an electronic communication – Wikipedia
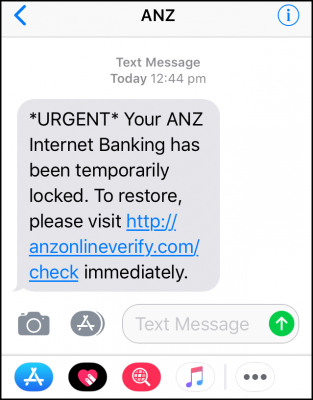
Phishing scams have been around for some time, however, as our everyday use of mobile devices and the internet in general has increased, so has the threat of phishing scams. Just recently my wife and I both received text messages on our iPhones, within a couple of minutes of each other, purportedly emanating from the ANZ bank:
- Note the urgent tone – specifically designed to frighten recipients into acting recklessly
- Note the lack of any form of personal address – no name, nothing which identifies the recipient
- Note the link – which is not secure (https) and when clicked will almost certainly send the recipient to a fake website
As it happens, my wife and I do bank with the ANZ. However, the ANZ Bank is huge in Australia, so if enough of these types of text messages are sent out at random, the chances of them hitting a large number of ANZ customers is very good. Of course, I didn’t click on the link but rather immediately rang the ANZ Bank to verify the status of my account and report this phishing attempt.
Phishing: What to Look Out For
These types of phishing scams are commonly delivered via two methods – email or text message. They will often appear to be from a legitimate source and usually include some sort of incentive – such as to claim money or a prize of some kind. Or, they will press some sort of urgent financial matter which requires the recipient to update or verify their details. The end goal is to entice you into voluntarily revealing critical information, such as banking or credit card details, often via a fake website specifically created for the purpose. If any of the following rules apply, then it will almost certainly be a phishing attempt:
- Rule #1: If an email or text message arrives unsolicited
- Rule#2: If an email or text message does not address you by your proper name
- Rule#3: If an email or text message includes spelling mistakes or grammatical errors
And remember– if it sounds too good to be true, it usually is!
Phishing: What To Do
- As per rule #1 above, start off by regarding any unsolicited contact from your financial institution as highly suspicious
- Under no circumstances click on any link or interact with the email or text message in any way
- Ring your financial institution immediately to verify the status of your account and report the phishing attempt
- Delete the text message or email as soon as possible
Bonus: The Microsoft Phone Scam
I must be considered an easy mark because I regularly receive phone calls from these lovely people with a distinctly offshore accent claiming to be Microsoft representatives. The way I deal with them now is, as soon as they’ve introduced themselves, I say… “No you’re not, don’t be so silly“, and that is usually followed by a loud click from the other end as they quickly hang up. How rude!
What these people will tell you is that your computer is transmitting Trojans, or some other similar nonsense, but they can fix it for you in a twinkle. Their end goal is to gain remote access to your computer in the hopes of maybe extracting critical information, such as passwords, banking or credit card details. Remember– institutions such as Microsoft will never contact you via an unsolicited phone call.
It’s a dangerous cyber-world out there folks, tread warily and carefully!
—



This surely hits home!!! Been getting emails from amazon.com saying my order is ready to ship, only trouble is I haven’t ordered anything. Got a phone call the other day from a guy saying my PC needed fixing and wanted access to my PC. We live in a very different world since the internet age.
Good day Jim. Seems the best way to help avoid phishing scams is by not supplying your email address to these services. This should also work for mobiles and land lines, as they must provide you with a valid call back number which you can verify.
The panic they provide is what generates their business. They rely on the a certain percentage of people who just click, click, click …. without taking a breath and thinking.
I can remember my first banking email scam. It was from an American bank informing me my account was compromised. I was amused a bank I had no dealing with sending me information. So I supplied bogus information to that link, and informed the security section of that bank of the fraud.
Today, should I be silly enough to click onto a phishing scam link, my protection software automatically warns me and blocks my attempt. Progress indeed.
My two cents when faced with panic message is to breath first, think, and refrain from clicking. Contact the institution via secure means to obtain information if there was indeed a threat, Mindblower!
I’ve had more than a few calls from “Microsoft Support” over the years. Depending on my mood I :
1. Inform them I don’t have a computer which throws them off script for some reason.
2. Play along with their instructions without actually doing anything. This can be amusing at times while they try to figure out what’s wrong. Especially when they ask leading questions.
3. Just say “No, you’re not.” and hang up.