Ransomware has quickly grown into one of the most prevalent threats today and is showing no signs of abating any time soon. We’ve already published several articles discussing methods for the prevention of ransomware, you can catch up with those articles by clicking the following links:
- Best Free Ransomware Protection
- WinAntiRansom Plus: Total Ransomware Protection
- Malwarebytes Releases Anti-Ransomware Beta
 When it comes to Ransomware, as with all forms of malware infections, prevention is always preferable over cure. However, nobody is immune from occasional lapses in concentration and with Ransomware’s increasing widespread proliferation there are bound to be more and more users falling victim. Security software companies have already developed a number of free tools to help users decrypt files which have been encrypted by Ransomware, however, these tools are generally fairly limited in their scope.
When it comes to Ransomware, as with all forms of malware infections, prevention is always preferable over cure. However, nobody is immune from occasional lapses in concentration and with Ransomware’s increasing widespread proliferation there are bound to be more and more users falling victim. Security software companies have already developed a number of free tools to help users decrypt files which have been encrypted by Ransomware, however, these tools are generally fairly limited in their scope.
A large part of the problem is that there are so many different Ransomware variations – currently more than 50 known Ransomware families and growing – and how quickly they are mutating. This makes it extremely difficult, if not impossible, for decryption tools to support every single type of Ransomware. So, the developers of these tools tend to concentrate only on a relatively small number of the most common strains. Here is a list of Ransomware decryption tools available for download from MajorGeeks: Ransomware Removal.
Emsisoft Ransomware Decrypter Tools
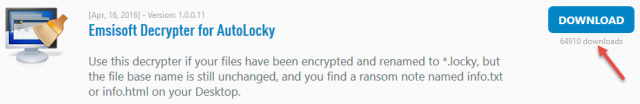
That rather elongated intro finally brings us to the point of this article. As far as I am aware, the largest collection of Ransomware decrypter tools is available from well respected security company Emsisoft. Emsisoft has developed 19 separate free decrypter tools each supporting a specific type of Ransomware. They are: ApocalypseVM, Apocalypse, BadBlock, Xorist, 777, AutoLocky, Nemucod, DMALocker2, HydraCrypt, DMALocker, CrypBoss, Gomasom, LeChiffre, KeyBTC, Radamant, CryptInfinite, PClock, CryptoDefense, Harasom.
Each tool is associated with a brief description to help users identify which particular strain he/she is dealing with:
- All 19 are available for download in one place, here: Emsisoft Free Decrypter Tools
If/when you visit the site, be sure to take a look at the numbers of downloads for each tool directly under the download buttons – quite alarming! We certainly hope that no-one falls victim to this most pernicious of infections but it won’t hurt to bookmark Emsisoft’s tools – just in case.
—


Dave,
The Emisoft Ransomware Decryptors would have to be run from an external source (presumably a flash drive) since they would be encrypted with everything else if they were on the computer’s hard drive(s). However if they are to run off a flash drive they can’t be installed since that would mean registry entries which would also be encrypted. Therefore it seems logical that Emisoft should make them portable. Is that the case?
I am certainly no expert but I suspect that there is an element of the user assisting the highjacked. I have had a number of incidents in the past few years. Ono W 7 proclaimed the computer infected and a direction to an MS phone number. I took a screenshot and shut down the PC. On restart I called a real MS number without starting the browser.
Another was last week on Firefox on Linux which said my computer was locked and gave a phone number. I panicked when I couldn’t close the tab or the browsers I shut down. After common sense returned I realised that my first responce could have been to yank the internet cord from my tablet supplying mobile data. Once again I recovered and deleted the browser history. The question is: can some link display a page and automatically execute a root blockage without some action of the user.
Once again I trusted my typing:
highjacked should be: highjacker.
Ono should should be: a popup on
Actally the mess up was probably the Google spell checker. I could wring it’s neck.
Bob, most all infections are user initiated. However, if the user visits a compromised site they may fall victim to what is known as a drive-by infection. A drive-by infection will usually take advantage of an out-of-date browser or operating system to deliver its malware. That’s why security experts are always advising users to keep all software up-to-date/fully patched.
Thanks Jim. Coming from my minutes old Pclinuxos install on my old laptop.