 On April 1st this year, US-based security company CloudFlare announced its new privacy-focused DNS service. For the uninitiated, CloudFlare has been involved in Internet security for quite some time and has risen to prominence mainly on the back of its DDoS mitigation service. In simple terms, DDoS (Distributed Denial of Service) attacks occur when multiple systems, usually connected through a botnet, simultaneously flood the target server with traffic, thereby causing it to crash. CloudFlare acts as a man-in-the-middle, identifying and warding off potential DDoS attacks. You will likely have come across CloudFlare at some time when browsing around the net.
On April 1st this year, US-based security company CloudFlare announced its new privacy-focused DNS service. For the uninitiated, CloudFlare has been involved in Internet security for quite some time and has risen to prominence mainly on the back of its DDoS mitigation service. In simple terms, DDoS (Distributed Denial of Service) attacks occur when multiple systems, usually connected through a botnet, simultaneously flood the target server with traffic, thereby causing it to crash. CloudFlare acts as a man-in-the-middle, identifying and warding off potential DDoS attacks. You will likely have come across CloudFlare at some time when browsing around the net.
Why is a privacy orientated DNS so important? DNS (Domain Name System) is essentially the Internet’s master phone book. It turns human-readable domain names, such as davescomputertips.com, into Internet Protocol (IP) addresses such as 67.202.70.109. For all practical purposes, every time you go anywhere on the internet, you start by interacting with DNS. Your Internet provider offers DNS as part of your service, but this also allows your provider to log your DNS traffic— in essence, recording your entire browsing history. Bottom line– ISPs can, and do collect and sell your browsing data.
CloudFlare DNS
What sets CloudFlare’s DNS service apart from other similar services, such as Google Public DNS and OpenDNS, is its heavy focus on privacy. In their official announcement, CloudFlare stated that they will never write the querying IP address to disk (very important) and will wipe all logs within 24 hours. To back this up, CloudFlare has committed to retaining KPMG, a respected auditing firm, to audit their practices annually and publish a public report confirming they are doing what they said they would.
Will CloudFlare DNS Prevent ISPs Logging Your Activity?
In short, no– at least, not right now. That’s because even though CloudFlare has done its part by including support for two main security (encryption) protocols, at present these protocols are not also supported by common software and/or devices that we use to interact with the Internet. Without the necessary encryption, some key information about your web-browsing habits, which is encoded into the bits and bytes that travel over the internet, can still be intercepted and read by your ISP.
CloudFlare DNS And Security
CloudFlare DNS includes support for the favored security protocol DNS-over-HTTPS, which encrypts data associated with web browsing as it flows online. Unfortunately, as mentioned earlier, support for DNS-over-HTTPS is not currently built-in to web browsers, operating systems, and devices. CloudFlare is, however, confident that DNS-over-HTTPS is the way of the future and hopeful that their initiative will encourage software developers to hasten the adoption of the security protocol as part of their products. In fact, Mozilla is already looking into making DNS-over-HTTPS a feature of its Firefox browser.
CloudFlare DNS And Speed
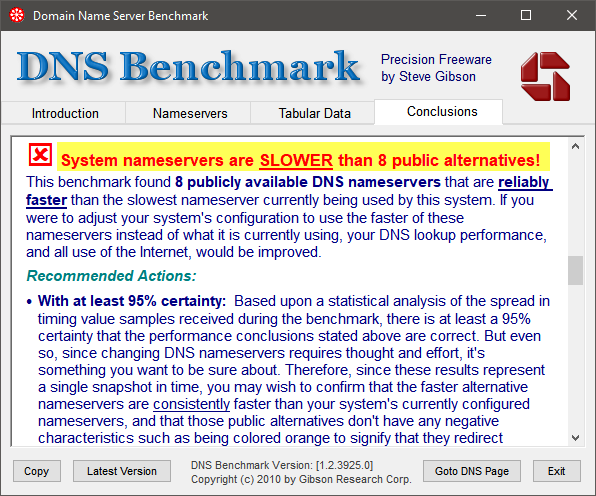
CloudFlare claims it is the fastest public DNS service available and, while this may well be true for users in the U.S., ping tests from my location in Australia do not support this claim. Admittedly, the differential in latency is minimal, just a millisecond or two, which is really neither here nor there. I also set up CloudFlare’s DNS as my default DNS resolver through my operating system’s settings and then ran benchmarks using Steve Gibson’s DNS Benchmark software, which reported eight public DNS servers as being faster than CloudFlare’s:
Again, the differential in speed is purely minimal and I would take security/privacy over a couple of milliseconds all day.
I must also take a well known tech writer to task over a comment he made in an article covering CloudFlare’s new DNS service where he stated that users’ ISP DNS servers are usually not the fastest. In my opinion, that is incorrect. The primary factor in speed is distance, as in distance between the connected device and the server. Maybe in the US, where ISP servers and public DNS servers are within a closer proximity, but outside of the US… I think not. Take my situation, for example– under normal circumstances it is highly unlikely that a server in the US, or any other part of the world, could possibly provide faster speeds than those in my local area. This was also backed up by ping tests and DNS Benchmark, both of which showed my ISP’s DNS as faster than CloudFlare’s.
By the way, CloudFlare came up with the following to support its fastest DNS claims:
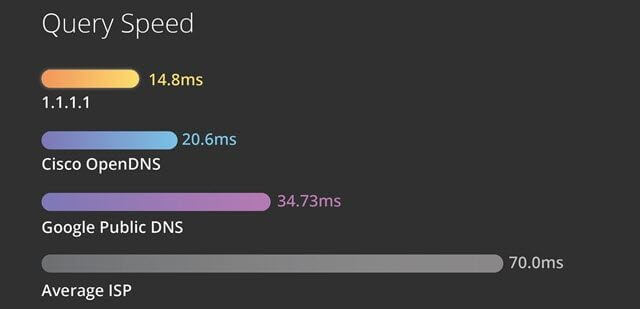
Would 70.0ms seriously represent the average for ISPs in the US? Here in Australia, if anyone’s ISP’s primary DNS address was pinging at anywhere near 70.0ms, I’d suggest they need to change ISPs. Mine pings at an average 24ms.
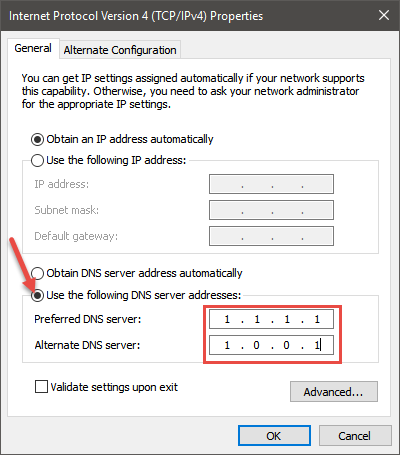
How To Change To CloudFlare DNS
CloudFlare DNS’s primary address for IPv4 is 1.1.1.1 and the secondary address is 1.0.0.1. For IPv6 they are 2606:4700:4700::1111 and 2606:4700:4700::1001.
For multiple networked devices it’s probably more expedient to make these changes through the router’s settings. For a single computer, however, these changes can easily be made through the operating system:
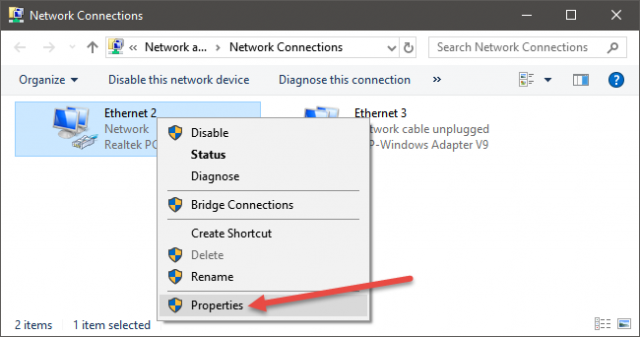
- Go to Control Panel and click Network and Sharing Center. In the new window that opens, click Change adapter settings (on the left).
- Right click on the default network adapter and select Properties:
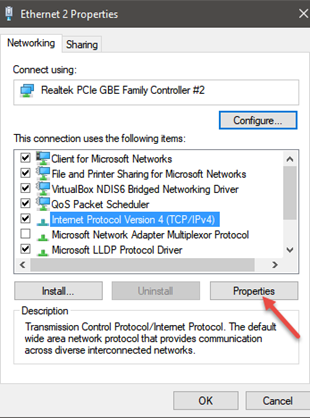
- Now, highlight (click on) the entry for IPv4 and/or IPv6 and then click the Properties button:
- Enable the option to Use the following DNS server addresses, type in CloudFlare’s DNS server addresses, and then click OK:
BOTTOM LINE
In today’s Internet, with ISPs and other companies freely collecting and monetizing users’ data, privacy has grown into a huge concern, and one can only applaud CloudFlare’s initiative to help mitigate these concerns. Let’s hope browser developers and the like take note and, sooner rather than later, implement the security protocols necessary for users to gain full value from CloudFlare’s efforts.
Cheers… Jim
—

good article! i changed to it and then ran dns benchmark from steve gibson. it came up in the fastest half dozen out of many. good find and thanks for passing it along.
Thanks for your comment clas, appreciated.
Hi Jim,
A damn good article with information also relating to us in Australia.
Thank You.
Cheers Jonno.