Here we go again with Tech sites scare-mongering and spreading misinformation. This time it’s all about Windows 10, UEFI, and Secure Boot. Some tech sites have been suggesting that Windows 10 will not work on UEFI systems unless Secure Boot is enabled, which is a complete misinterpretation of the facts. Based on what little information is available, here’s what’s really happening – and even this is not yet set in concrete:
Windows 8 and UEFI Secure Boot
It has nothing to do with the operating system (Windows 10) per se and is all about the “genuine” logo licensing terms. To explain that further: Microsoft offers all manufacturers the opportunity to apply a “Designed for Windows [version]” sticker to their products. In order to obtain those rights, manufacturers have to agree to a set of conditions, as outlayed by Microsoft under its logo licensing terms.
Do you recall a similar furor regarding Secure Boot when Windows 8 was due for release? When Microsoft announced that UEFI Secure Boot would be a mandatory feature under its logo licensing terms there was a massive outcry from disgruntled users because of the potential for preventing dual booting or even installing a different operating system.
However, following the public outcry, Microsoft amended the terms for its “Designed for Windows 8” logo to include a solution to the potential problem: Microsoft also mandated that every system MUST include a user-accessible switch to turn Secure Boot off. Peace reigned again.
Windows 10 and UEFI Secure Boot
Now, on to Windows 10, and this is where the confusion comes in: Microsoft has intimated that, under the Windows 10 logo licensing terms, it will no longer insist on the inclusion of an option to turn Secure Boot off, leaving it purely optional – as in up to the manufacturers whether they want to include the option or not.
That’s it, that’s what all the fuss is about. Let’s take a look at the implications logically:
- Due to the competitive nature of the market, I believe it’s pretty safe to assume that many manufacturers would choose to include an “off switch” for UEFI Secure Boot even if they are no longer forced to do so.
- Even in the event that certain manufactures choose not to include the option to turn Secure Boot off, only new mobos and systems built and distributed by those particular manufactures under the “Designed for Windows 10” logo would be affected – and, even then, Windows 10 will still work fine.
- Existing (pre-Windows 10) UEFI systems all include the option to turn Secure Boot off. So, those who utilize the upgrade path to existing hardware would not be affected at all.
In a nutshell, Windows 10 will still work fine on both BIOS and UEFI systems, and regardless of whether Secure Boot is enabled or not. Plus, of course, this is all supposing Microsoft does go ahead and drop its mandate forcing manufactures to include an option to disable Secure Boot, we probably won’t know for sure, either way, until RTM (Release To Manufacturing).
I really don’t see an issue here, a mountain out of a mole hill.
Dual Booting Windows 10 & Linux
Could a permanently enabled Secure Boot mean the end of Linux on a Windows PC? No. UEFI is a global standard that Microsoft has no ownership over. Therefore, if Linux distributions include compatibility for UEFI, they’ll be able to run without a problem in a “secure boot” environment. <source>
The rise of mandatory, locked Secure Boot could create a problem for smaller Linux distributions or custom Linux systems—but the Linux Foundation Secure Boot System is a generic loader signed by Microsoft that should allow any Linux system to boot on PCs with Secure Boot enabled. <source>
The latest versions of popular Linux distributions, including Ubuntu, Mint and Fedora, already install just fine on a Windows PC that has Secure Boot enabled, and this trend can only widen. After all, developers will always have the incentive to make their product as compatible with as many machines as possible.
I guess there is always the possibility that Microsoft may eventually stop signing these Linux loaders thus preventing them from functioning in Secure Boot mode, however, I believe that’s a highly unlikely scenario. I’m a half-glass-full kind of person. 🙂
Seriously, after the Windows 8 debacle followed by the Windows 8 to 8.1 upgrade shambles, Microsoft really needs Windows 10 to succeed and I can’t see the company making any decisions that would likely impede that success and/or damage its sagging reputation even further.
Final Word
The jury is still out on just how much value Secure Boot actually adds from a security point of view, but that’s another story for another time. To quote security expert Bruce Schneier… “I think this [secure Boot] is just another piece of security theater that will inconvenience many and benefit no one.”
- FOOTNOTE: If you’d like to participate in a discussion about this topic, feel free to join us on the DCT forum here: Windows 10 first impressions?

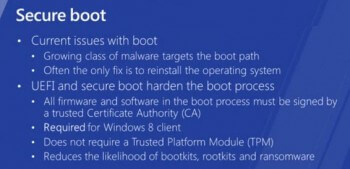

Jim. To clue me into what might seem as very silly, just what is this “Secure Boot” in laymans terms, Mindblower!
Explaining Secure Boot in layman’s terms is near an impossibility MB. Essentially, it is a system of validation that ensures only certified software can be loaded. In the simplest terms; the firmware (UEFI) contains a set of signatures and will refuse to run any software which is not signed with one of those signatures.
MS explains it thus:
Microsoft need to be given the Order of the Boot beware Windows 10 is a massive scam
I hate that MS insisted that manufacturers make Secure Boot run by default because once you have purchased a computer, you should be able to do whatever you want with it and not have Big Brother trying to prevent you from doing so!
Having said that, I have still left Secure Boot running for reasons which escape me at the moment. Because if anyone wanted to run a malicious disk on my PC, I’m pretty sure they would know how to disable Secure Boot anyway! And with it running, my PC will not even boot from a Genuine Retail version of Windows 7 Home Premium! So I think my next job will be to disable it once and for all. LOL.
I agree 100% Sherri. I would not buy a new UEFI system unless it came with an option to disable Secure Boot.
My laptop is a windows 8.1 machine. Being an engineering student I have assignments to be done on Ubuntu. I tried installing Ubuntu on the machine but it did not work.Now i have got an update of windows10, should I go ahead with the update? or will it worsen the matter? My sole concern is that I want my machine to be able to be a dual boot machine.
Secure Boot is part of UEFI and completely separate from the operating system. So, Windows 8 or Windows 10, it will make no difference. If your laptop was able to dual boot with Windows 8 it will still be able to dual boot with Windows 10.
My concern is mentoring! You see, in prep for win10, Microsoft has already installed software through updates.
Will Microsoft be gathering data from all pc’s and/or devices? How venerable will we be? If they do collect data, will it be all or random? What data would be interesting to Microsoft?
I ask this because the internet is becoming more and more dangerous everyday and I don’t want to be spied on…..do you?
>>> “How venerable will we be?”
venerable or “vulnerable”? i think you meant vulnerable, teaman … pls verify your content by relegating google as your ally. thanks 🙂
Hi Jim,
A customer of mine just purchased a new pc. I need to clone the new hard drive to an SSD. Problem is it will not boot to the boot cd I have. The secure boot enabled is locked and I can’t change it. Any way around this? I want legacy. Thanks!
This is a huge part of the problem Linda – UEFI was supposed to be universally standardized yet not only do we see completely different versions between manufacturers but also between different models from the same manufacturer. Why the heck they can’t just standardize all UEFI settings so they are ALL the same is beyond me.
I would need to know the make and model of the PC you are working with, and the motherboard make and model might also be required.
The rise of mandatory, locked Secure Boot could create a problem for smaller Linux distributions or custom Linux systems—but the Linux Foundation Secure Boot System is a generic loader signed by Microsoft that should allow any Linux system to boot on PCs with Secure Boot enabled.
note the bit that says “signed by Microsoft” Microsoft owns the secureboot mechanism that is dovetailed into UEFI and since Microsoft own the signing key they can revoke that key if they decide that an alternative operating system threatens their profit margins.it doesn’t matter that the Linux foundation has a copy.
so to say that Microsoft does not own UEFi is only a half truth, they “own” UEFI by virtue of the fact that they hold the signing key to secureboot. no signing key = non functional hardware(unless you can bypass secureboot/uefi or a mechanism exists enabling you to create your own signing key)