There’s been a lot written recently regarding a vulnerability known as “FREAK”, much of it involving unnecessarily scary rhetoric. The truth of the matter is, for Windows users anyway, the only real risk is (or was) pretty much restricted to Internet Explorer. Both Firefox and Chrome in Windows are not susceptible to the FREAK vulnerability.
What is FREAK?
FREAK is an old yet newly discovered vulnerability involving SSL/TLS technology which is used to establish an encrypted connection when transmitting sensitive information online, such as credit card and banking details.
About 15 years ago, the United States Government made it illegal for companies to export software which included strong encryption – that is, encryption which couldn’t be readily cracked by its own security and intelligence agencies.
Although those rules have since been relaxed, most internet servers and web browsers still include the old encryption algorithms built-in, even though they are now rarely used. However, it was recently discovered that many internet-based systems can easily be fooled into enabling the old insecure encryption systems rather than using the newer ones. This then is the flaw that’s now known as “FREAK”.
How Bad is FREAK & Who is Affected
In practical terms, the level of risk presented by FREAK is being reported as relatively low.
Windows users should note that, contrary to some misinformation being reported, both Firefox and Chrome browsers are NOT vulnerable to this flaw. On the other hand, Internet Explorer is vulnerable, or I should say was... Microsoft has now issued a patch via Windows Updates which rectifies this bug. <https://technet.microsoft.com/library/security/MS15-031>
All Windows users, especially those who do not have automatic updates enabled, should apply the latest round of Patch Tuesday updates as soon as possible.
Apple/iOS users should note that these platforms are vulnerable to the FREAK flaw. Google has already patched the version of Chrome for Mac to disable the problem and Apple has now issued updates for OS X (10.8, 10.9 and 10.10 – Mountain Lion, Mavericks and Yosemite), iOS, and Apple TV, which include a patch for the FREAK flaw. <source>
If you are running any of the aforementioned Apple platforms, it is strongly recommended that you apply the appropriate updates as soon as possible.
How To Check Your System for the FREAK Bug
Regardless of platform or browser, you can visit this site: https://freakattack.com/clienttest.html to find out if your system is vulnerable to the FREAK attack or not:
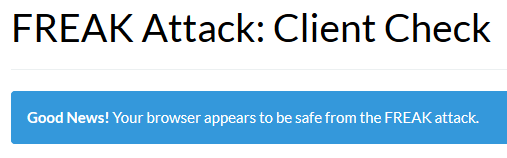
- Here is the message for Firefox and the patched Internet Explorer running in my Windows 8.1 system:
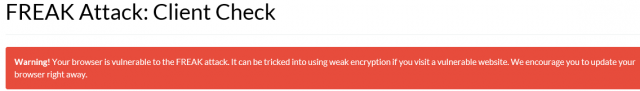
- And here is the message if your system is deemed unsafe:
*NOTE: Browsers are not the only software involved, some related 3rd party programs can also leave the system vulnerable:
Even if your browser is safe, certain third-party software, including some anti-virus products and adware programs, can expose you to the attack by intercepting TLS connections from the browser. If you are using a safe browser but our client test says you’re vulnerable, this is a likely cause.
For example: Avast free users are consistently reporting that the software’s Web Shield component is triggering a warning on the FREAK Check site. The way to overcome this would be to disable Avast’s Web Shield until the problem is patched.
Good to see involved parties moving to patch this vulnerability quickly, makes for a pleasant change.


I have never heard of this one but IE11 checked out OK. Thanks for the tip. Daniel.