
OK . . . you’ve decided that you want to make your purchase from AcmeExplosives.com (after all, Wiley Coyote gets his dynamite from there, so he trusts it).
And it has an SSL Cert that you’ve checked out (Part 1). So what’s this “layered security” business and what more do I have to do?
Well, how far you want to go on this really depends on how much you want to use the particular vendor and also how much you want to protect your credit card account number. There may come a point where further scrutiny just doesn’t make sense. Drop it and either reach a comfort level with the site or go on to the next one. Each of us may have different levels of scrutiny we want to apply.

You definitely want to make sure that at least you implement the SSL check in Part 1. If the site handles the transaction (as opposed to redirecting you to PayPal) and doesn’t encrypt your purchase transaction, that’s IT! Don’t make the purchase there from that site. You need go no further. When you’re on the checkout page, look up at the address bar . . . no SSL, just close out the tab/window and certainly don’t press “Submit”.
So what about if it transmits via SSL? Is that enough? NO! Remember those unscrupulous CA’s?

So you should at least make some of the checks listed here in Part 2 and to be offered in Part 3. How much you do, as stated above, really depends on your own judgment about trust. How far do you need to scrutinize? Your call . . . it’s that “comfort level” thing. Don’t waste your time going overboard, but do enough that it will give you that “comfort level”.
OK . . . now let’s get into some of the things you can do after your selected site (the one where you want to use your CC for a purchase) has “passed” the SSL test.
(Note: Identifying whether or not the site harbors malicious code is the easy part, is very objective, and I’ll give you some tools to do that in Part 3. But the harder part is deciding whether or not you TRUST the site, so I’ll deal with that first, because if you don’t trust the site, it’s moot whether or not it contains malicious code.)
The first thing you want to check is the “Contact Us” information. (And if the site doesn’t even have a “Contact” page, and I’ve seen plenty of product selling sites that don’t, you DEFINITELY don’t want to make a purchase there.)
Typically, a “Contact Us” link can be found easily in either the links along the top or the footer of a site:
Some sites have only a mechanism for emailing, and that’s fine if it’s only something like a blog. But if it’s a site that offers a product to purchase, then you’re going to want much more than just an email contact form.
That’s because if you buy something, you’ll want to know just exactly where the physical address of the vendor is. That’s for several reason’s itself.
First, if you’re not satisfied with the product and want your money back, or worse: never get it!!, just an email might not do it. What is there to ensure a response? And perhaps most importantly: What about if I want to return merchandise? Where would I send it to?
As far as ONLY an email address in a contact form, it could be a fake email address, disposable . . . whatever. How many times have I heard, “I emailed them dozens of times but never heard back from them.” The vendor, in this case, can take your money and run and you’ll never hear from them again:
It was very cheap so I didn’t lose that much money (I paid for a year’s hosting in advance), but the moral of the story is: You get what you pay for, and also I should have done more thorough due diligence to begin with.
I emailed them several times and got all the emails back with the dreaded “Undeliverable, blah, blah, blah . . . “ notice.
And contacting any kind of government agency to register a complaint without a physical address of the scammers that are the subject . . . won’t even pass the laugh test. You’re likely to get: “Sorry, we can’t do anything about it unless you have a physical address.”
Indeed, if there’s not a physical address given, it’s likely that it IS a scam.
(Granted, some Credit Card companies will forgive the charge IF you notify them within a certain time period AND have a reason that fits their policy . . . usually thirty days and an affidavit detailing your reason for this, but these mechanisms are iffy at best, a hassle many times, and very often you’re needlessly putting your money at risk. Now PayPal usually withholds a payment for thirty days, so that may be the preferred method of payment IF that’s an option. But this all assumes you have made a judgment on the situation, or resolved it within thirty days. Many unscrupulous vendors will just give you the runaround for OVER thirty days so that you won’t make a claim for a refund in that time period. Best to just flat out avoid that situation by first doing a little due diligence on your own as outlined here.)
And perhaps more importantly, check out the physical address and phone number they give (Google is your friend.) One time I checked out a physical address and found that it was a vacant lot, another time I found that the address didn’t even exist. And several times I found out the phone number was fake. True stories.
A vendor’s contact address:

If the site lists a bogus address or phone number, would you trust them? My own opinion: I would NOT give people like that my CC number, even if they DID show it was transmitted via SSL.
OK . . . so now we have ascertained that they have an SSL and do have a valid address and phone. My recommendation: Take it a few steps further because SSL and valid address and phone numbers won’t necessarily reduce your risk as much as it would if it were coupled with a few other checks. This is that “layered security” I talked about in Part 1. And remember, we’re talking about sites that sell stuff (not blogs), sites you don’t know about, and sites that aren’t mainstream well known vendors. Again, this is for the Mom and Pop and boutique vendors that you maybe turned up in a Google search and you’re going from there.
I’ll repeat: Don’t waste your time checking sites like PayPal, eBay, Amazon, TigerDirect, etc.
OK . . . what should you scrutinize next? Well, not so fast! Remember we were going to look at their contact form? Some will show a P.O. Box. That’s pretty much useless. If there IS a contact form and it ONLY shows a P.O. Box, it might as well be a vacant lot for all the good it’s going to do you. My recommendation: Stay away from that vendor.
Indeed, the UK has a law that says that anyone operating a commercial web site FROM THE UK that offers a product for sale MUST somewhere on the site show their physical address.
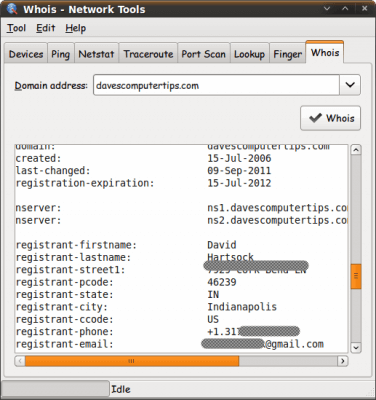
Which leads me to the Whois info. Whois searches reveal a lot of basic info about a site, like who is the “registrant” (typically, the owner but not always), when they first went on line (registered the domain name), when the registration expires, the registrant’s physical address (unless they use a “Privacy Service”, a very important issue that I’ll discuss in a bit), who to contact with complaints (typically an email address, but not always), the phone number of the registrant, and a lot of other geek info that often is misunderstood and that you needn’t pursue.
What you’re primarily interested in is who the “owner” is and what is the physical address/phone number, and whether or not it matches any of the info on the site itself. Sometimes it doesn’t but there’s a reasonable explanation . . . and the site should gladly explain.
But if there’s not a reasonable explanation or what you get is suspicious or a bunch of “blah, blah, blah . . .”, then my recommendation: Don’t use that vendor.
A “whois” check can be done for free by several web sites, “Domain Tools” is one of the more prominent and trustworthy: http://whois.domaintools.com/ . But there are many many other whois services out there, and most of them are FREE. In fact, if you find one that wants to charge you for the information, go find a FREE one . . . there are plenty.
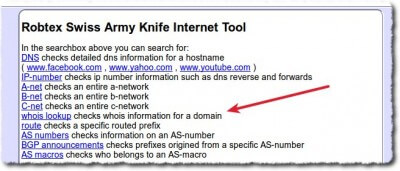
“Robtex” ( http://www.robtex.com/ ) is another good one:
For Windows, there is a FREE piece of software called “Sam Spade” ( http://majorgeeks.com/Sam_Spade_d594.html ):
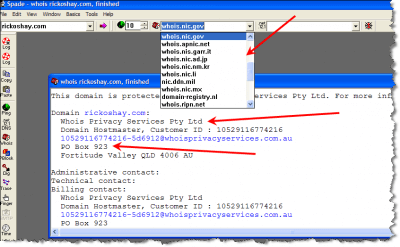
This particular search shows three important things . . . and there’s a fourth if you go to the site itself (“rickoshay.com”)
First, you can see by the drop down that there are a multitude of “whois” servers. Sam Spade allows you to choose which one you want to use.
Some are good, some are not so good. Some will provide you with the information you’re looking for in an easily readable format, others won’t. It’s always best to do a few at least.
Secondly, you can see that this guy has his info hidden behind a “Privacy Service”. That’s not necessarily bad because sometimes these people operate their business out of their house and justifiably don’t want crazy people bothering them at home. (And we know that there are a lot of crazy people on the Internet . . . stalkers, for example.)
But when a commercial site selling a product has their whois info hidden behind a privacy service, that IS cause to raise an eyebrow. There might be a perfectly reasonable explanation, but you need to find out what it is.
Finally, you’ll see that this guy lists a P.O. Box . . . a definite No-No for a site selling anything (though that may be the mailing address for the privacy service . . . whois info is not always clear, which is why it’s best to use more than one.)
And then if you go to that site (rickoshay.com), you’ll see a bunch of search links only, and no real content. Usually that indicates a “parked” site, which usually (but not always) means that this domain name is up for sale by the owner. If this WAS your vendor, being “parked” now is a pretty good sign that this person is about to make off with any money he/she has gotten.
(BTW, that particular site was once a “web design” site and the owner sold “web site design” services. I have no idea what’s going on with it now, except the site no longer has any content.)
Finally, on visiting the site you can get a flavor of what the place is like . . . just as if you were walking into a brick and mortar store and getting a general impression of the place.
Does the site have a professional look? A bad design does not necessarily mean it’s a “bad” site, but it’s certainly a red flag to look further.
Poor English is another red flag. Not necessarily an indication of a scam, but definitely a prompt to dig further. (A lot of spam is written with poor grammar and spelling . . . a strong indication that it’s spam.)
Are the prices too good to believe? If so, then it may be prudent to look into it further. Had I taken better note that my ripoff host had ridiculously low prices, I might have avoided losing my money.
The truism that “If it’s too good to be true, then it probably isn’t true” applies here.
So if it’s designed poorly (e.g. navigation around the site is difficult), has poor grammar, and the prices are outrageously low . . . probably best to move on to another. Your call, but I would be too uncomfortable with this myself.
If you’ve gotten this far and the site is still viable to you, then I will be giving you some tools to check for malicious code and another way to protect your account number in Part 3.
