 We’ve all been through the scenario; we purchase a shiny new PC and experience that tinge of excitement and anticipation as we rush home to set it up. We get home, plug it in and boot it up, only to be confronted by a plethora of manufacturer installed software… what is commonly referred to as bloatware.
We’ve all been through the scenario; we purchase a shiny new PC and experience that tinge of excitement and anticipation as we rush home to set it up. We get home, plug it in and boot it up, only to be confronted by a plethora of manufacturer installed software… what is commonly referred to as bloatware.
Every manufacturer is guilty, there have even been specialist software applications designed specifically to rid new machines of this pestilence – e.g. Decrap My Computer and PC Decrapifier. For a long time we considered the practice more of an irritation and inconvenience than a security risk, then along came the likes of Superfish and eDellRoot. Now, an investigation by security firm Duo Labs has proven beyond doubt that these pre-installed manufacturer-based programs do indeed represent a major security risk.
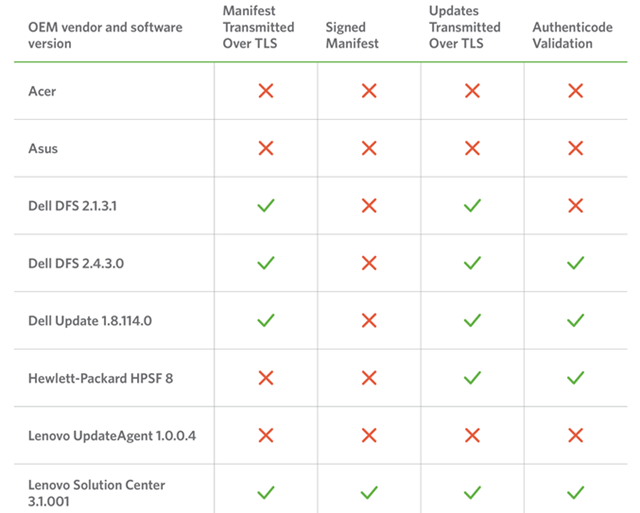
Duo Labs concentrated its investigation on the most common tools included with OEM software… third party updaters. The security company discovered that at least one (or more) of these updater tools is included in the default configuration of every single new machine, and the majority are wide open to exploitation.
Duo Labs summarized:
Some vendors made no attempts to harden their updaters, while others tried to, but were tripped up by a variety of implementation flaws and configuration issues. In total, we identified and reported twelve unique vulnerabilities across all of the vendors.
The security company’s investigation also identified a number of concerning trends:
- Every vendor shipped with a preinstalled updater that had at least one vulnerability resulting in arbitrary remote code execution as SYSTEM, allowing for a complete compromise of the affected machine.
- Vendors often failed to make even basic use of TLS, properly validate update integrity, or verify the authenticity of update manifest contents.
- Vendors sometimes had multiple software updaters for different purposes and different implementations; some more secure than others.
- The large attack surface presented by ancillary OEM software components makes updater-specific bugs easier to exploit in practice by providing the missing pieces of the puzzle through other tools bundled with their systems.
And most worryingly; the level of sophistication required to exploit most of these vulnerabilities is next to zero – in other words, any hacker, even those on “L” plates, would have no difficulty exploiting them.
- Read Duo Labs article here (including a link to download the full report): Out-of-Box Exploitation: A Security Analysis of OEM Updaters

We are rushing head long into a crisis with all our modern conveniences. Just look at the problems with Lexus automobiles in N.A. (and likely in other parts of the world) All our connected devices were designed with little thought for security. Now we, and indirectly the manufacturers are going to suffer.
I have no doubt these manufacturers have developed good security systems and will use this “new” feature as a selling point in the future went peoples devices are being compromised.
Couldn’t agree more Tom: https://davescomputertips.com/iot-insecurity-the-biggest-consumer-threat-ever/