TrueCrypt is a very powerful program that you use to create virtual encrypted disks (which are basically just files on your hard drive that can be mounted as if they’re disks, complete with unique drive letters). You can also encrypt entire partitions or hard drives and encrypt entire USB flash drives. For most people, a simple encrypted volume on the hard drive will be all that’s needed. For those who own laptops that have sensitive personal or business information on them, full-drive encryption is recommended. Likewise, if you back up sensitive data to a USB flash drive, you’ll want to encrypt the whole drive.
I’ll show you how to install and configure TrueCrypt to create a simple encrypted volume that you can use to store your information securely. Mac OS X and Linux users: TrueCrypt works for you, too. Installation and configuration steps should be similar, but be aware that I’m showing the Windows version.
First, go to http://www.truecrypt.org/downloads.php and download the version you need. Save it to a convenient location. Double-click the TrueCrypt setup icon and we’re ready to go. Click on Run when you see the security warning:

Accept the terms of the license agreement. (It’s an interesting read if you care to read it.):

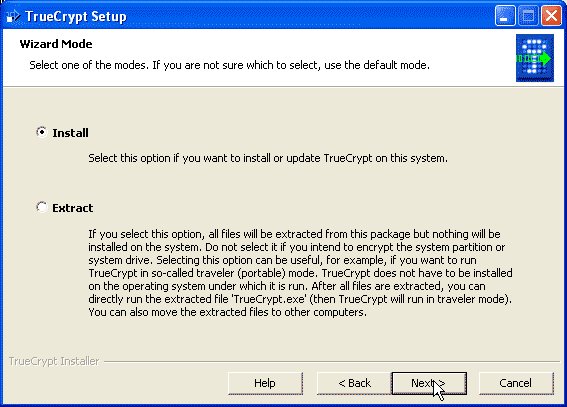
On the next screen, click Next to accept the default Install option:
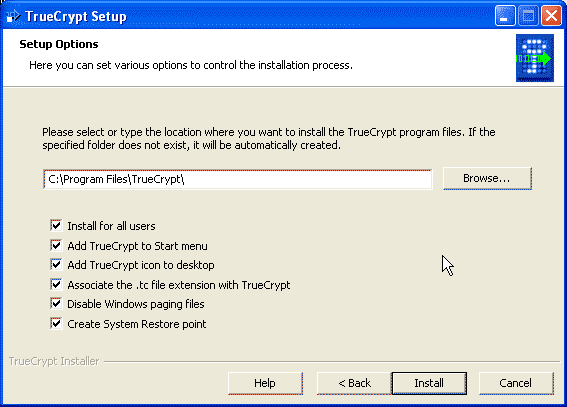
Accept the defaults on the next screen and click the Install button:
You’ll get a message telling you TrueCrypt was successfully installed and you’ll be asked if you want to restart. Click OK on the first message, and NO on the second if you want to examine the installation log screen:

Go ahead and restart your computer (you’ll see a message saying that you can’t close the installation wizard until you restart. Click yes). When your computer comes back up we’ll get down to work setting up an encrypted volume. Go ahead, I’ll wait..Zzzzz…
Oh! I see you’re back. OK. Double-click the TrueCrypt icon on your desktop and you’ll see this screen:
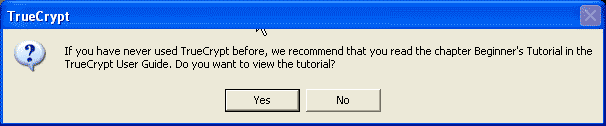
You absolutely want to read the Beginner’s Tutorial, so click Yes. It’s going to tell you just about everything I show you here, but it has a few tips you’ll want to know. The tutorial will open in your browser, so you can follow along and continue setting up TrueCrypt. When you see this screen, click on Create Volume:

On the next screen, accept the default by clicking Next:
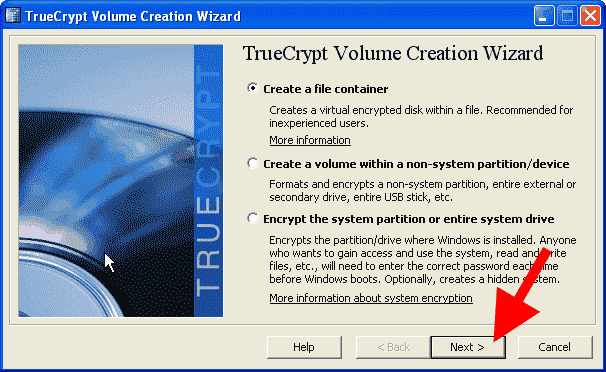
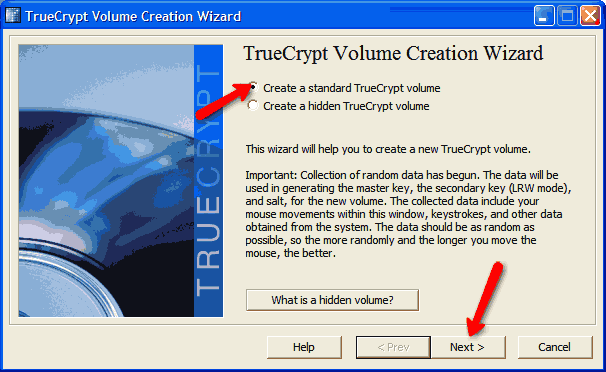
For now, we’re just going to accept the default and create a Standard TrueCrypt Volume:

On the next screen, just type a name for your volume. It can be any name you want. Then click Next:

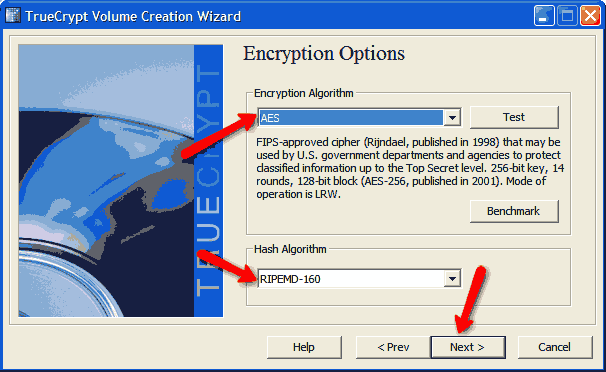
On the next screen, just accept the defaults; it’s stuff for Geeks like me who want to tweak things:
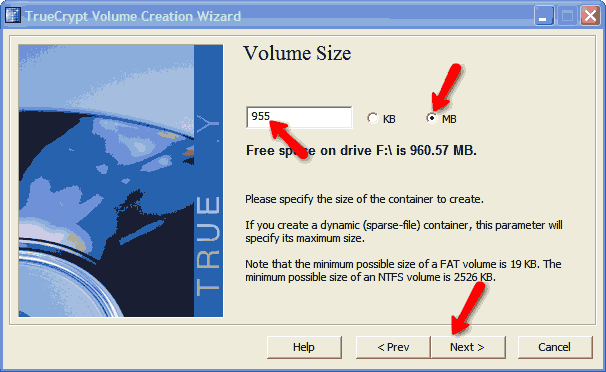
Next, select the size of your volume. I chose 50 MB, but you can set it to anything you want up to the maximum space available on your drive:
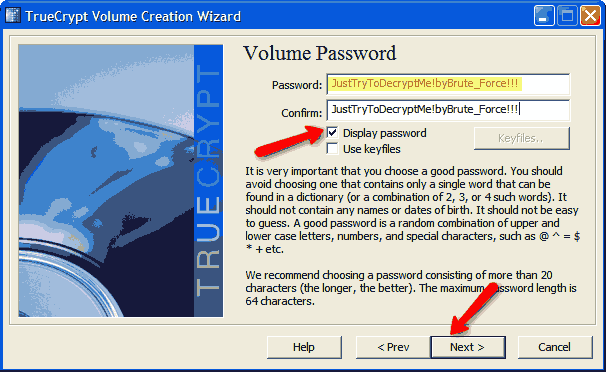
Click next and you’re going to be asked to set a password. Read the screen and you’ll see it gives the same advice that I promote.
Don’t worry about the Use keyfiles option for now; I’ll explain that later. You can go ahead and check the Display password box if you want; it might make it easier for you to enter a long password twice. Yes, you want a long password, though you don’t have to make it 20 characters. If you don’t, however, you’ll get this warning:

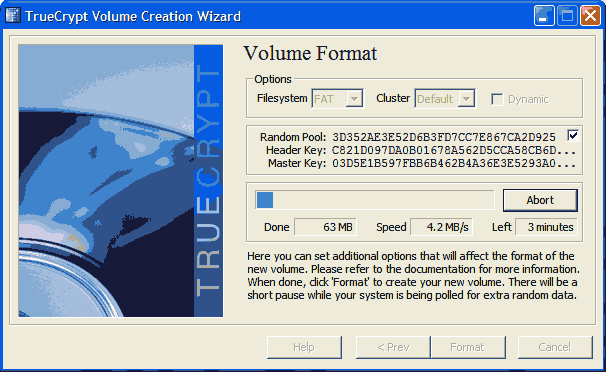
On the next screen, you’ll be asked to select your file system. I recommend NTFS, as that is what Win7/Vista/XP uses as default. You can safely ignore the note at the bottom of the screen. The randomness of the numbers that you see flashing by are already so high as to make cracking the encryption of your volume virtually impossible.

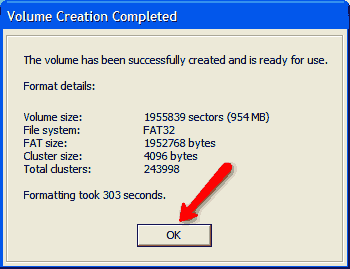
You’ll see some things happen and then you’ll be presented with these two messages:
and
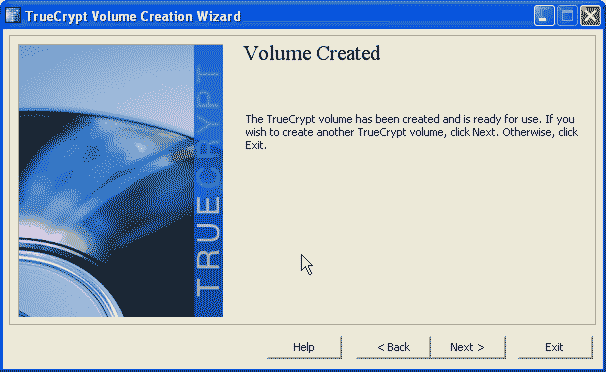
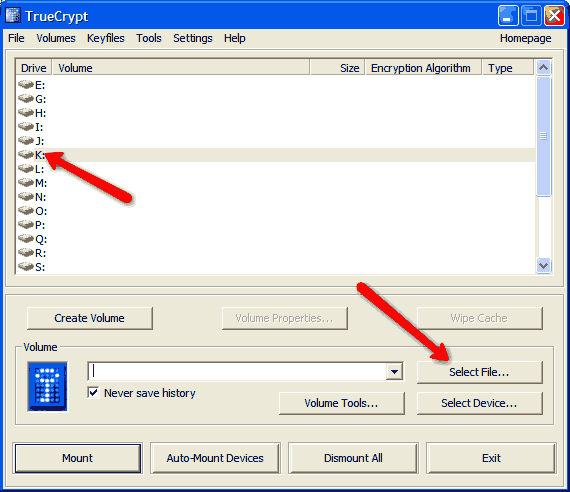
Go ahead and click exit and you’re ready to start using your new encrypted volume. Go back to the main window and click Select File:

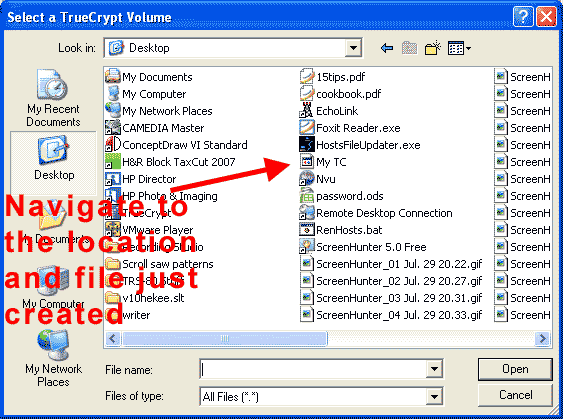
Choose the name for the volume you just created:
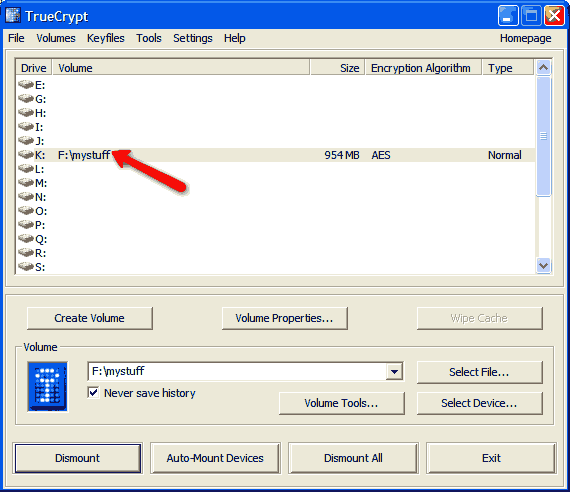
Back at the main screen, select a drive letter you want to use and click Mount. Mounting refers to the computer associating a drive letter with a location, in this case the TrueCrypt volume you just created. You’ll be prompted for your password.

Enter it, and your TrueCrypt volume (in my case, Z:\) will be mounted. Now, you can safely Exit the program. Don’t worry, your drive will stay mounted until you restart.
You can save files to your TrueCrypt volume just like you would save them to any other drive. Whatever you store there will be encrypted and decrypted on the fly as long as the drive is mounted.
When you shut down your PC, the volume will be dismounted, so the next time you start up, you’ll have to run TrueCrypt and mount your volume again. If you don’t turn off your PC, be sure to manually dismount the volume; otherwise, anyone who gains access to your account will have access to your TrueCrypt volume. If you dismount it and someone gains access to your account, they’ll have to know your TrueCrypt password to see your encrypted files.
Using Truecrypt to encrypt a USB drive
Data breaches caused by lost or stolen USB flash drives seem to be the latest trend (see below). So, rather than showing you how to encrypt a hard drive, I’m going to show you how to encrypt a USB flash drive so that anything you store on it will be unreadable to anyone but you (or someone who has the passphrase). I’ll cover full-drive encryption on hard drives in Part 3.
TrueCrypt allows you to encrypt entire partitions, complete hard drives, or USB flash drives (which, after all, look like hard drives to the system). Most of you won’t need to encrypt your PC’s entire hard drive–a simple encrypted volume where you store your sensitive information is usually sufficient. For those who own laptops that have sensitive personal or business information on them, full-drive encryption is recommended. If you travel frequently with a laptop, then full-drive encryption is essential. Likewise, if you back up sensitive data to a USB flash drive, you’ll want to encrypt the whole thing. Flash drives are small and easily lost or stolen; in fact, USB flash drives have been the cause of serious data breaches. The Privacy Rights Clearinghouse (PRC) states that over 93 million data records of U.S. residents have been exposed due to security breaches since February 2005. According to Beth Givens, Director of the PRC, “The latest trend to show up is the loss of memory sticks.”
Creating an encrypted USB flash drive is a little different than creating an encrypted hard drive because it has to be portable: i.e., the TrueCrypt program must reside on the flash drive. That way, no matter where you plug it in, you’ll be able to open your files. Any flash drive should work, but you want to be sure to copy any data off of it before you encrypt it because the procedure I’m about to give you will erase everything on the drive.
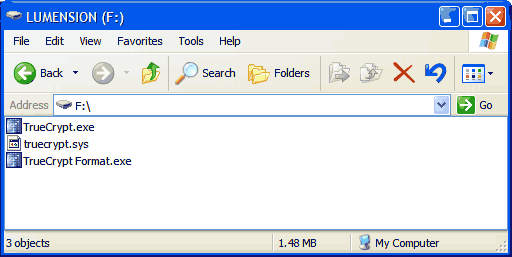
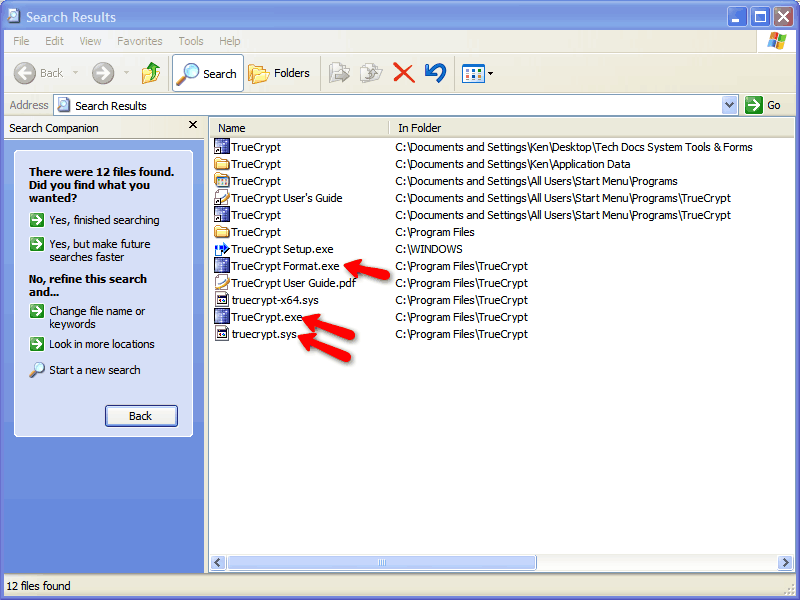
The first thing you need to do is locate the following three files: TrueCrypt Format.exe, TrueCrypt.exe, and truecrypt.sys. The easiest way to find them is to search your hard drive using “truecrypt*.*” as the search term.
Copy these to your flash drive. In my case, the drive letter was F:\.
Now, run TrueCrypt Format.exe. Leave the default “Create a standard TrueCrypt volume” radio button selected, then click Next:
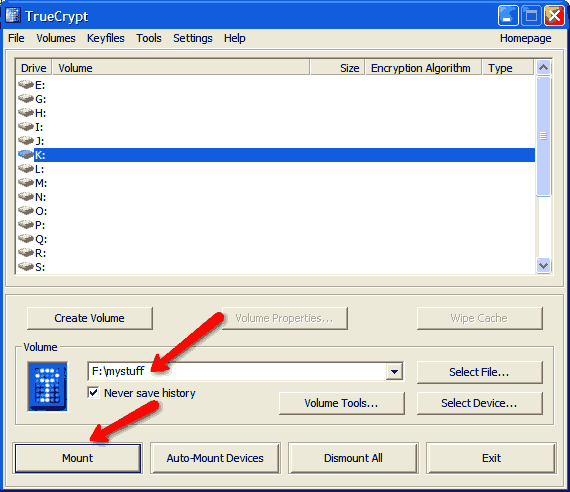
After you click next, you’ll see the device selection screen. Leave “Never save history” checked and click “Select File”:
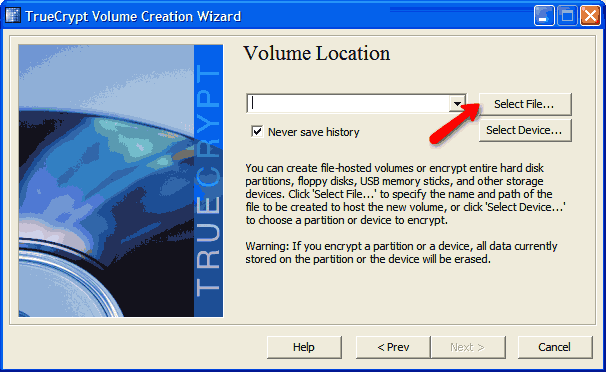
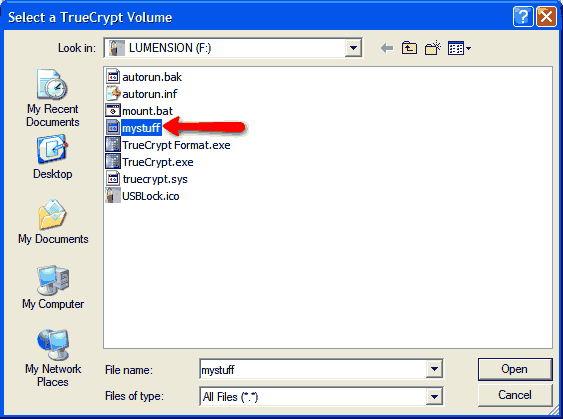
Navigate to your drive letter, if necessary, enter the name you want for your encrypted volume in the filename box and click Open:

Note that your drive and filename is now shown as the volume location. Go ahead and read the information on the screen and click Next:

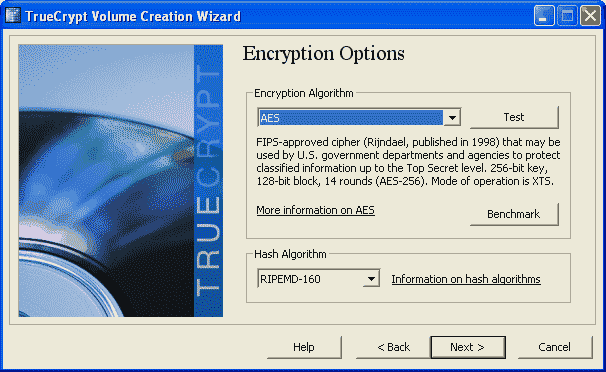
The default Encryption Options are more than sufficient, but you can change them if you want. If you don’t want to change them, just click Next:
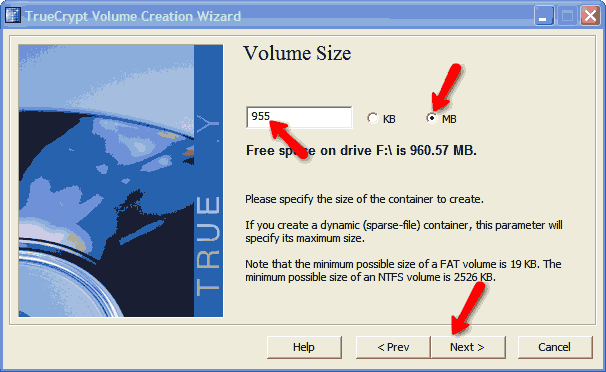
Now, you’ll specify the size for your encrypted volume. You need to leave the TrueCrypt files in unencrypted space. In version 6.0a, these files take up 1.48 MB on your drive. I recommend you set the volume size to 5 MB less than what TrueCrypt reports as free space. In my case, free space is 960.57 MB, so I’m going to specify my volume size as 955 MB. Click the “MB” radio button and enter your volume size in the box. Click Next:
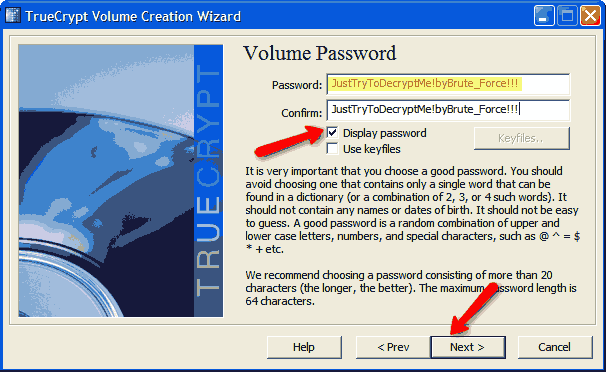
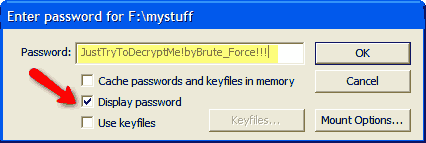
Now, you’re going to enter a password. Read all of the information on the screen and note that 20 characters is recommended. You can check the “Display password” box to make it easy for you to enter your password. I recommend you write your password down or take a screen shot and store it in a safe place—if you forget your password, there’s no way to recover your data. The password I entered is 34 characters, upper/lower case and special characters. Click Next.
Now, you’ll be prompted to select your file system. I chose the default, FAT, but you can also select NTFS if you wish (MAC and Linux users will have other options). Click the “Format” button:

The screen will begin to change and will report the progress of the encryption. This may take awhile, depending on the size of your drive. Just let it go until it’s complete:
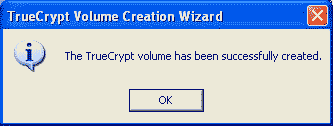
You’ll see this report. Read it and click OK:
At the next screen, click Exit and you’ve successfully created an encrypted flash drive volume.

To use your new encrypted flash drive, just plug it into any USB port, open up the drive letter and double-click truecrypt.exe. Select any available drive letter and then click Select File:
Select the name of the volume you created:
Note the drive letter/file you selected and click Mount:
Enter your password. Click “Display password” if it helps you to enter your password correctly. Click OK when you’re done:
Your encrypted volume is now mounted and you can minimize TrueCrypt:
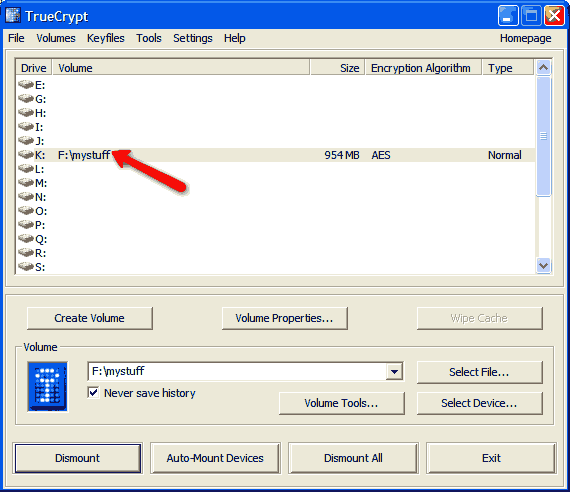
Your mounted drive will show up in My Computer. The K:\ drive is the encrypted drive; F:\ is the unencrypted portion of the flash drive:

Anything you store on the K:\ drive (or whatever drive letter you’ve chosen) will be encrypted.
When you’re finished storing data, access the TrueCrypt screen again, select your encrypted drive letter, and click “Dismount:”
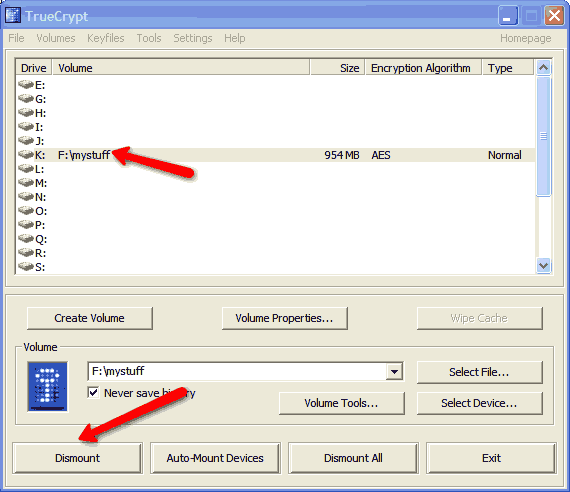
Once you’ve dismounted the drive, it’s safe to remove it. A word of caution: Never try to remove the flash drive from the system until you’ve dismounted it—you can lose data or corrupt your encrypted volume.
Hi Ken ,
I have 2 questions about True Crypt
Qn1. Can I open 2 True crypt Volumes simultaneously , on the same computer , both the Volumes are having the same PW. If so, will there be any problem in copying files from one to the other.
Qn2. If I Encrypt one Partition of the HDD and later want to De- Crypt the same Partition , how can it be done