When the popular encryption software TrueCrypt shut up shop one of the main contenders to take over the mantle has been VeraCrypt, which is based on the original TrueCrypt code – you can catch up with more on the history here: VeraCrypt Rises from the Ashes of TrueCrypt.
However, one of the main issues with VeraCrypt has been that it hasn’t included support for existing TrueCrypt volumes. Volumes created by TrueCrypt could not be mounted in VeraCrypt and the only way to overcome this was to decrypt the volume using TrueCrypt and then encrypt it again with VeraCrypt.
That all changed with the recent release of an updated VeraCrypt version which now includes support for TrueCrypt volumes:
UPDATE December 30th 2014 : VeraCrypt 1.0f is out with many new features and enhancements. The most notable ones are the support of mounting and converting TrueCrypt volumes, and the speedup of the mounting process through the manual selection of the correct PRF algorithm.
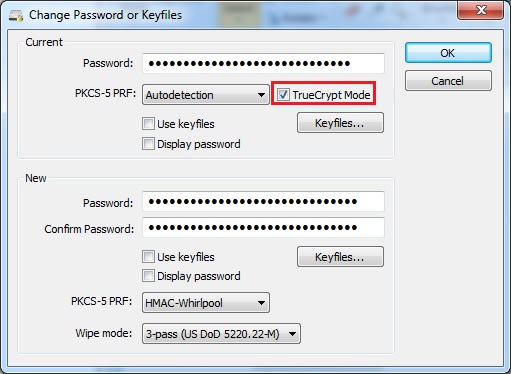 This means that existing TrueCrypt volumes can now be mounted using VeraCrypt and the developers have also integrated an option to easily and quickly convert TrueCrypt volumes to VeraCrypt volumes, so it is no longer necessary to decrypt an entire volume using TrueCrypt and then encrypt it again with VeraCrypt in order to create native volumes supported by the VeraCrypt software.
This means that existing TrueCrypt volumes can now be mounted using VeraCrypt and the developers have also integrated an option to easily and quickly convert TrueCrypt volumes to VeraCrypt volumes, so it is no longer necessary to decrypt an entire volume using TrueCrypt and then encrypt it again with VeraCrypt in order to create native volumes supported by the VeraCrypt software.
This latest release makes VeraCrypt an even more attractive proposition for those TrueCrypt devotees who have been holding out for a worthy successor.
- More details and download here: https://veracrypt.codeplex.com/#

Interesting, I’ll check VeraCrypt out one of these days since the whole TrueCrypt deal left me with some doubts about its robustness.
Been looking for a replacement for True Crypt. Installed VeraCrypt tonight and created me a 10GB container for my document files. It runs almost like True Crypt. Daniel.
I tried it, but I’m not impressed by the speed required to mount volumes: it’s way slower than TrueCrypt.
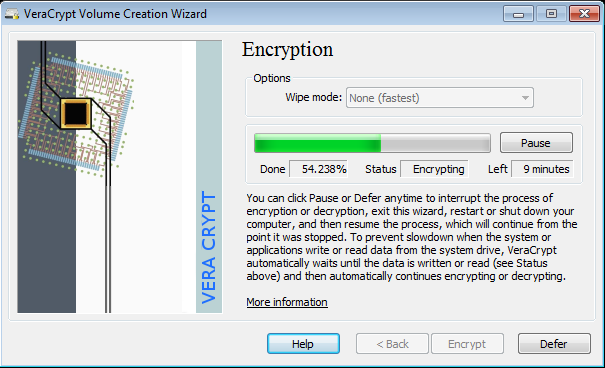
It is a little slow in mounting a volume. I think their is a way to speed up the mounting process but I am a little hesitant to start clicking on anything and lose my data. It took a little over an hour to format a 200GB HD and about 15 minutes to my 10GB container. Not quite as good as True Crypt at this point but at least someone is working Vera Crypt, hopefully for a long time. Daniel.
All the reliable evidence suggests that there is no problem in continuing to use Truecrypt and in an conversion routine, particularly when working with volumes that have hidden volumes, there is the possibility of data becoming corrupted. Certainly I would see this as a sensible replacement when creating new volumes but unless a windows update causes truecrypt to stop working there doesn’t seem much point to it. Speed is also an issue because I simply have all my data volumes encrypted and so they need to be mounted each time I intend using them – the volumes are 500gb each and truecrypt does this almost instantly – I would want to experiment with vera crypt on a spare drive first.
Its the number of iterations. Security vs speed… you decide.
I don’t quite understand. Certainly the iterations is an issue on formatting, converting headers, etc. How does that affect mounting?
I am experimenting with Vera Crypt now with my 200GB hard drive. It takes about 60 seconds to mount my 10GB container, maybe someone can explain why it takes this long to mount. I usually do not encrypt the whole drive but will create containers for storing sensitive data. Daniel.
As I understand it, that slowness is intentional. It solved one of the concerns with the audit that had to do with iterations. Increasing those iterations makes the software more secure against brute force attacks.
VeraCrypt uses 327,661 iterations of the PBKDF2-RIPEMD160 algorithm for system partitions, and for standard containers and other partitions it uses 655,331 iterations of RIPEMD160 and 500,000 iterations of SHA-2 and Whirlpool, which makes VeraCrypt slightly slower at opening encrypted partitions.
Thanks Michael, that explains certain actions of Vera Crypt.
Note: Converting system partitions encrypted with TrueCrypt is not supported.
Is there a way to convert hidden volumes?
Copy off all important data from the hidden partition by burning to DVD disks (temporary, they can be destroyed)
Format your HDD to remove all data with your favorite wiping software, one pass is fine.
Recreate your new encrypted setup using Veracrypt – System – Decoy + Hidden System.
Copy data into Hidden System from DVDs and destroy DVDs