There is no doubt that the malware landscape has changed dramatically over the past decade. In today’s internet world, malware is more often than not linked with the criminal element and, because of the massive potential for ill gotten gains, is well financed and well organized. In short, today’s malware is big business! But are Security Software Companies managing to keep up with today’s ever increasing malware variants or is a fresh approach perhaps required?
When it comes to identifying malware; the traditional signature-based detection, heuristics, and cloud-based recognition employed by antivirus programs work well only up to a certain point. The polymorphic malware however, which is constantly changing [morphing], still maintains a distinct edge over this current methodology.
Although the appearance of the code in polymorphic malware varies with each “mutation,” the essential function usually remains the same. For example, a spyware program intended to act as a keylogger will continue to perform that function even though its signature changes. If the malicious program is discovered by an anti-malware vendor and its signature is added to a downloadable database, the anti-malware program will fail to detect the rogue code after the signature has changed, just as if a new virus, worm, Trojan or spyware program has emerged.
<credit: whatis.com>
It now appears that a solution to this problem may be in the making, compliments of an Australian security researcher who presented the results of his work at the annual AusCert conference held last week in Australia. Silvio Cesare, a doctorate candidate from Deakin University in Melbourne, has developed a system which identifies new malware strains by their heritage. Rather than focusing on scanning at the byte level, Mr. Cesare’s technique looks at small ‘structures’ woven through the malware code, which are common to each family of malware.
Traditional antivirus is good at something, but signatures aren’t very good at detecting entire families of malware because if you change the malware a little bit, it changes the byte-level content of that malware. Even moderate changes to the malware don’t change the structures very much. Using structures, you can detect approximate matches of malware, and it’s possible to pick an entire family of malware pretty easily with just one structure.
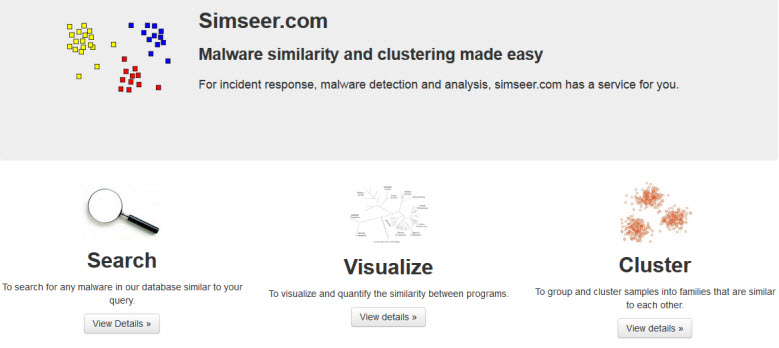
To this end, Mr. Cesare has created a free online service (Simseer) which performs automated analysis on submitted malware samples and shows just how similar they are to other submitted specimens.
According to the website, Simseer detects malware’s control flow, which changes much less than string signatures or similar features… and polymorphic/metamorphic malware variants generally share the same control flow. Simseer has identified more than 50,000 strains of malware to date, and that number continues to grow. Hopefully, malware and security analysts will take note and utilize the Simseer service to help with their research… and ultimately, we’ll see security software developers adopting Mr. Cesare’s approach.
I close with a quote from the well respected security company and anti-virus vendor Kaspersky:
The biggest threat is posed by the huge mass of unknown malware. Effective protection may not exist to combat these threats when they first appear.
<source>

Thanks Mr. Hillier for info. Very interesting online service. Also thanks Mr. Cesare for that.
Another informative article, thank you Jim, and good to see an Aussie in the forefront of cyber protection.
Thanks to Mr. Silvio Cesare for his good work.
Thanks Jim So there may be light at the end of the tunnel ??
Nice article, Jim. Great break-through by Silvio Cesare.