
The DNSChanger malware was first discovered around 2007, it has since been widely distributed in a variety of forms and infected millions of computers worldwide, including around 500,000 in the U.S. alone. Mac OS machines are equally susceptible.
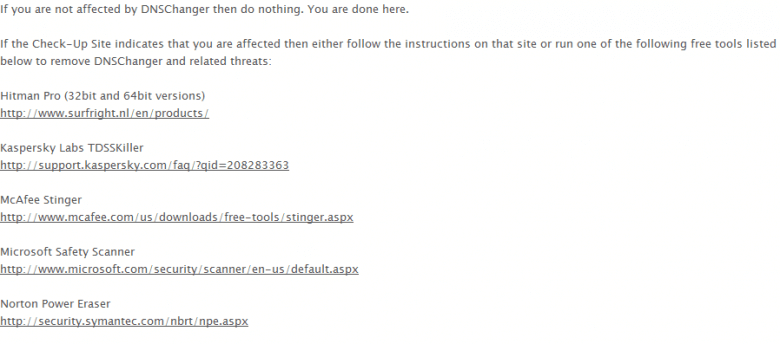
Specialist malware detection and removal tools have since been developed to help combat the threat, and most brand name anti-virus products now also include specific definitions for detection and removal.
Simply shutting down the rogue DNS servers immediately would have left people using infected PCs without any Internet connection, so the FBI opted to temporarily legitimize the bad servers thereby allowing affected users time to disinfect. The servers were initially set to go offline on March 6, but many systems haven’t yet been disinfected so, earlier this month, the deadline for pulling the plug on the servers was extended to July 9.
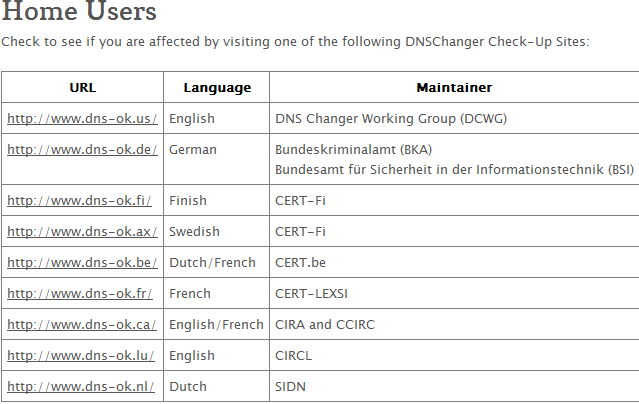
Apart from running anti-malware utilities to detect and [possibly] remove the DNSChanger trojan, Windows users can now go to a special page where they can check to see if their machine is infected.
Simply click on a link appropriate to your language. The test is very quick, and if the results do indicate your machine is infected, just follow one of the links below the table to download a free program which is known to successfully remove the the bug.
Check for DNSChanger infection HERE
A free removal tool for Mac OS X users is available HERE.
More information regarding DNSChanger and steps taken by the FBI HERE
I found the explanation to be a little confusng. I still don’t know if I have it or not.
Thanks Mate
Hi David – I wouldn’t worry too much mate, chances are your machine is not infected. If your machines was infected, you’d probably be aware of problems by now.
I’ve now added an extra link to the ‘check’ page to make it clearer. Simply go to the that page: http://www.dcwg.org/cleanup.html – and click on the first link in the table (English). You’ll see the result almost immediately.
Cheers…Jim
Thanks Mate.
David
HI Jim,
Guess I dodged that Bullet!
Thanks
Jim,
I have a colleague who is unable to access the internet from his home desktop and his laptop is very slow. I am thinking it may be the DNSchanger. Is there a downloadable program to check and fix an infected computer or is he limited to reformatting?
Thanks again for all your efforts.
Ray
Ray – There are plenty of free tools which will identify and remove the DNSChanger infection – but they won’t reverse changes already made to DNS settings in both the OS and connected router. Suggest reading through here: http://dns-ok.gov.au/information.html (includes a good list of available tools as well).
If a machine is infected with DNSChanger it will now not be connecting at all, so the slow laptop would likely be clear. That doesn’t necessarily mean the laptop would be free from other infections though.
As far as the desktop is concerned: Being unable to connect to the internet can be caused by any number of issues, if your colleague would like any assistance, we can help resolve this on the DCT Forum.
Cheers… Jim