Winners Announced!
[message type=”info”]
ASCOMP Secure Eraser Pro Giveaway Contest!
This contest has now expired. Winners will be notified by eMail.
- Gerallt Bath
- Edward Dawson
- Robert Rozijn
- Larry Rydel
- Mickey Fradenburg
Congratulations to the Winners and Thank You to everyone who participated!
[/message]
 ASCOMP Secure Eraser Pro
ASCOMP Secure Eraser Pro
ASCOMP has generously offered five (5) licenses for their Secure Eraser Pro software to five lucky Dave’s Computer Tips (DCT) readers. Each license is currently valued at $20.00 (US) each.
There is a free version available for personal use only, but the Pro version removes ads and allows for tech support and multiple business licenses. Read on to learn more about the features of this flexible product.
System Requirements
This product is compatible with the following operating systems:
Secure Eraser Professional
Secure Eraser uses the most renowned method of data disposal and overwrites sensitive information in such a sure way that it can never be retrieved – even with specialized software. Our multiple award-winning solutions for definitively destroying data also eliminate any cross-references that could leave traces of deleted files in the allocation table of your hard drive.
This easy-to-use Windows software will overwrite sensitive data even up to 35 times – regardless of whether they are files, folders, drives, recycle bin or traces of surfing. You can also delete files that have already been deleted, but this time for good.
Secure Eraser not only overwrites using random data, it offers the approved US Dod 5220.22-ME and U.S. DoD 5220.22-MECE standards from the US Department of Defense, the German industrial standard and the Peter Gutmann standard. All deletions are logged in details upon request. ~ ASCOMP
Overview
Secure Eraser includes a local help file in PDF format. It is well laid out and easy to understand. I much prefer this to having an online help system where you must be connected to the Internet to get immediate help if you need it.
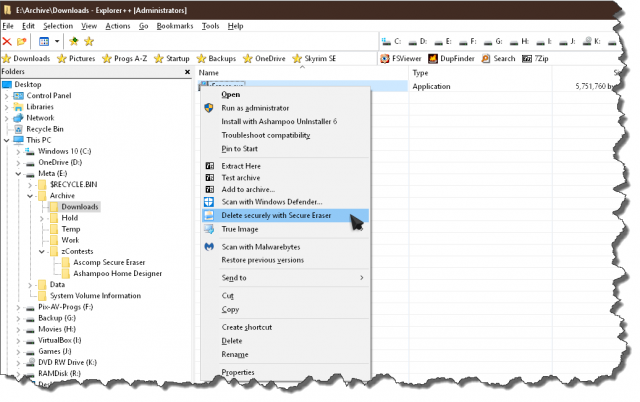
Secure Eraser adds an entry to your Context menu for easy access to the program.
Secure Eraser Features
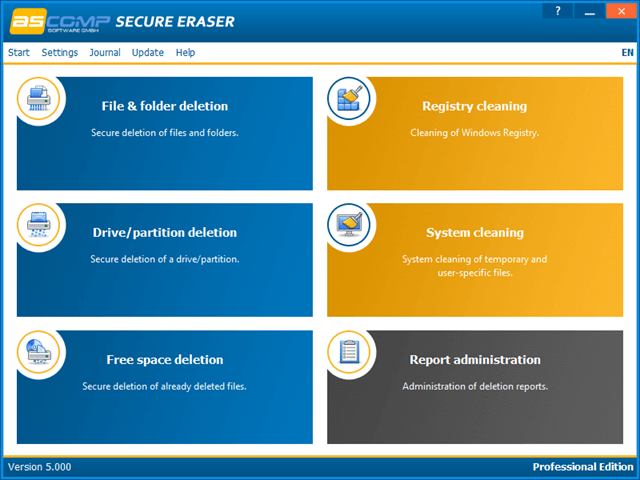
Secure Eraser includes the various types of file/folder deletion that you would expect from software in this genre. It also includes a Registry Cleaner and a System Cleaner. Anyone who has followed my articles over the years knows that I do not support Registry Cleaners too strongly. I believe the risks outweigh the potential benefits. The System Cleaner included in this package is a simple, straightforward tool. A more dedicated cleaner such as CCleaner or PrivaZer might be a better choice as it will give you many more options and features. However, it is a nice addition and has been included if you choose to use it.
Note: DCT ran a CCleaner to PrivaZer comparison article a while back and you can read it at CCleaner vs PrivaZer – Which is more effective?
A search on DCT for PrivaZer will bring up several articles on the subject.
All in all, I would say that Secure Eraser is a complete solution for those who have the need or desire to truly and fully delete the contents of their drives.
How to Enter the Contest
We’d appreciate it if you’d take a moment and submit a comment telling us why you’d like to win Secure Eraser. However, submitting a comment is not required to enter this contest and will have no bearing on your chances.
For your chance to win, simply enter your name and valid eMail address in the spaces provided below, then click Enter Contest. After your entry is accepted you will be presented with options to share the contest on Twitter and/or Facebook. For each person that enters the contest as a result of your share you will earn two (2) extra entries!
Sharing the contest on social media is completely voluntary, but is encouraged.
Competition Rules:
- To enter, simply submit your name and a Valid eMail address. Your address will not be shared outside this site
- You must submit a VALID eMail address. We need to contact the Winner, so disposable eMail addresses will not be eligible
- Additional entries may be earned by voluntarily sharing on Facebook and/or on Twitter
- Shortly after the contest ends, the winner(s) will be chosen at random
- Winner(s) names will be posted on this giveaway page. Please check back here to see the winner(s) name announcement!
- The winner(s) will be notified by eMail at the eMail address used to enter the contest – be sure to use a valid eMail address that you check regularly
- Winner(s) must claim their license within five (5) days. After the five (5) day period, unclaimed prizes will be distributed at DCT’s sole discretion
- Entrants agree to allow DCT to communicate with them via eMail using the address provided by the entrant when entering the contest
[contesthopper contest=”73183″]
Good luck to everyone!!
—

Excellent article Richard. You truly nailed it. Love the way you mentioned the link between CCleaner and PrivaZer. Find this is an added bonus of having the help file stored on your computer in PDF. Can easily toggle and remain off-line. Have not tried it yet, but intend to do so soon, Mindblower!
Thanks, Mindblower!
Glad you liked it,
Richard