 Security company G DATA has released its regular half-yearly malware report for the first half of 2015. Among the findings, researchers discovered a 64.8% spike in new malware strains as compared to the first half of 2014. This averages out to 12 new strains per minute. In all, the total number of malware strains this year is expected to be well above the level of 2014, with the U.S., China and France heading the list of most malicious/fraudulent websites hosted.
Security company G DATA has released its regular half-yearly malware report for the first half of 2015. Among the findings, researchers discovered a 64.8% spike in new malware strains as compared to the first half of 2014. This averages out to 12 new strains per minute. In all, the total number of malware strains this year is expected to be well above the level of 2014, with the U.S., China and France heading the list of most malicious/fraudulent websites hosted.
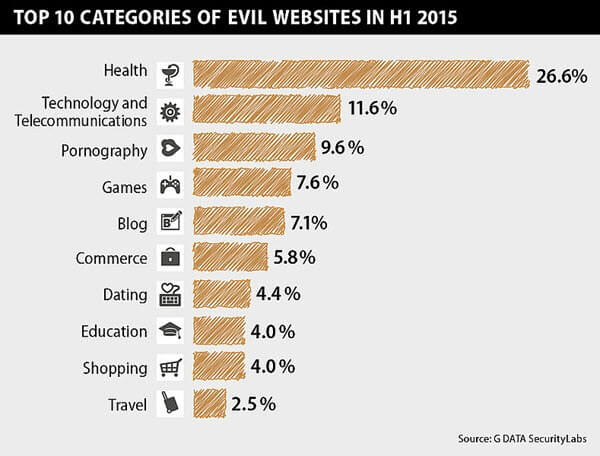
The report breaks down the incidence of malicious websites based on content type and contains a couple of surprises, with Health topping the list, almost 3 times the percentage attributed to pornography sites:
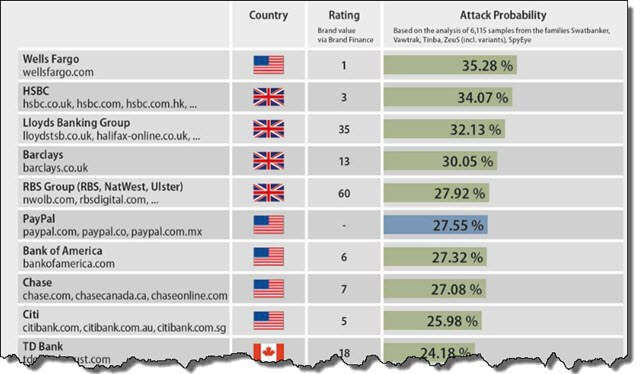
The report also looks closely at the banking industry with researchers finding that Wells Fargo was the financial service most frequently targeted by banking Trojans – the Swatbanker family being the most prevalent trojan during the 6 month period.
“About three-quarters of Internet users are conducting their financial transactions online, and cybercriminals have recognized this huge opportunity for malicious attacks,” said Andy Hayter, security evangelist for G DATA. “Not surprisingly, because of this, we’re seeing a significant increase in attacks from banking Trojans for the first time since 2012.”
While the news that numbers of malware, fraudulent sites, and banking trojans are on the increase is certainly alarming, it’s not exactly surprising. However, there is one piece of vital information contained within the report which everyone should take note of:
- Exploits for vulnerabilities are now being integrated into exploit kits after just a few days. Users who do not keep their systems up-to-date will easily fall victim to cyber criminals.
It’s something the security fraternity has been advising for a long time – keep all your software always up to date – and with the time frame between vulnerability exposure and active exploitation closing rapidly, it could never be truer or more critical.
- View the full 16-page G Data report here: G DATA Half-Year Malware Report: Jan-June 2015 (PDF)

So True! I have many clients who never update their systems and I continue to remind them of the risk. Other than doing it for them people just need add it to their life. Just like taking the trash out or getting your car a tune up this needs done. Very important article to share.